WPEngine Credentials Exposed
Update 1 (3:10pm CST on Dec 10th): WPEngine is working with federal law enforcement as part of their investigation into the breach. They are also working with a ‘leading cyber security firm’, presumably someone who specializes in incident response and forensics. They haven’t provided any further details about the incident yet.
Original post:
About an hour ago WordPress hosting company WPEngine sent out an email to their customers asking them to change their passwords.
The passwords they want you to change are the user portal, sFTP, your WordPress database password, your original wp-admin WordPress account and any password protected installs and transferable installs.
We have reached out to WPEngine and received this response from Eric Jones:
As we indicated in our notification to customers at WP Engine, the security of our members’ personal information is a top priority. In response to an exposure involving some of our customers’ credentials, we are taking proactive steps to mitigate the issue. While we have no evidence that the information was used inappropriately, out of an abundance of caution, we have initiated an investigation and notified customers that we are invalidating five passwords associated with their WP Engine account. Customers were provided with specific instructions on how to reset each of them.
Again, we are committed to the protection of our customers’ personal information. As we learn more from our ongoing investigation, we will provide updates to our customers if we learn of information that affects them.
Additional information and any future updates about this event are available at http://wpengine.com/infosec
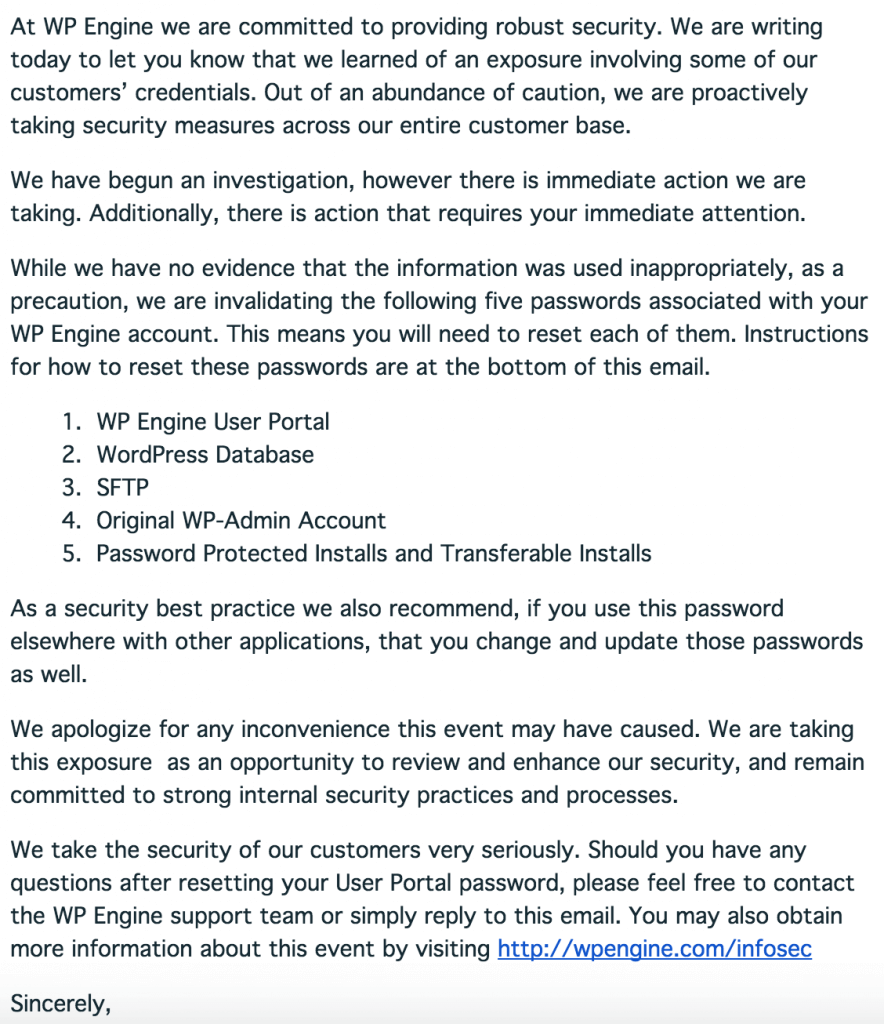
A snapshot of the email sent about an hour ago is below:
We will update this post as we learn more.
~Mark.

Comments
10:55 pm
Thanks, I have changed my passwords
The best,
P.L.
11:01 pm
Thanks Mark, you guys are on the ball! Thankfully I'm not hosted with WPEngine but nonetheless, I'm personally appreciative of you and the team's efforts, keep up the awesome work!!
8:23 am
I am also not hosted on WPEngine. Nonetheless Thanks mark for head up.
11:35 pm
Good to hear they react quickly to protect those WordPress installations, thanks for the heads up.
12:59 am
I have some additional information on this - I'd like to discuss in further.
2:45 am
@John The only update we have seen so far is this:
"Update 12/10/2015 3:53am Central: In an attempt to provide more assistance to the recommendations below, you can find updated step-by-step links on how to reset your passwords here"
So not really much more details other than a link to reset the passwords.
1:15 am
Great for WP Engine for picking it up so quickly, I still think they're awesome. (As well as Wordfence for spreading the news so quickly)
Linda
2:14 am
So, this is only for people hosted by WPEngine. I am hosted by BlueHost, so am I correct in assuming I do not need to change anything?
Thanks.
2:46 am
@Carlyn That is correct. This was something that happened to WPEngine on their servers. Only WPEngine customers need to be concerned.
4:42 am
No comment on the XSS vuln you fixed in your own plugin today?
https://plugins.trac.wordpress.org/changeset/1304473/wordfence
6:02 am
Are you referring to the one we discovered, reported, and fixed ourselves?
tim
1:02 pm
Yes, but you've not announced it anywhere, not advised customers that there's an active XSS vuln, and that patching is important? I get WP-Engine hack is huge, and this shouldn't take away from it, I've relied upon your reporting for some time, but I would've expected you to at least note the XSS issue somewhere publicly.
1:32 pm
I understand your concern but can I clear something up? The vulnerability was discovered by a researcher here and patched in the plugin release we sent out, all within a very short time. In addition to addressing the plugin issue we also patched it on our servers so that if you were running an earlier version of Wordfence, it still couldn't be exploited. That's without you updating anything. It's not anything I would call 'active' because it was immediately remediated with the patch on our servers. We also added the information about it to the release notes and then spread the word about the release on twitter and facebook. I hope this helps you understand what happened. Should you want to discuss this further you can email us at genbiz@wordfence.com where we will be happy to answer any of your questions.
7:26 am
Ahh, it being internally patched and inactive makes all the difference. I still thing you should write a blogpost about it even so, considering your audience, detailing what you found, and how you fixed it, is of great interest :)
4:07 pm
Thanks, just want you to know that we had an extensive internal conversation about this. We will likely share more in future.
4:43 am
I received an email alerting me to the problem with a link to this article. This article mentions instructions on how to change the passwords...all five of them. Where are these instructions? They're not in the email.
5:43 am
Check WPEngine's post on their site.
tim
5:01 am
Such a bad news struck to WPEngine. Luckily, I am not hosted there but I know many friends who are. Will send them this news over their way.
Thank you!
5:13 am
I'm new to Wordpress. I have installed Wordfence in my development environment but not deployed the website. Is Wordfence the same as WPEngine? I don't understand the connection. Does this mean I have to change my password?
6:47 pm
Hi,
Unless your website is hosted with WPEngine (https://wpengine.com/), your data is completely safe.
No need to worry! WordFence is just being on the ball and alerting those who potentially might be customers of both WordFence and WPEngine.
5:14 am
WP Engine is literally the best. They were on top of it right away and they're always quick on support. I've never had any issues since I left the bargain hosting companies and went to them. I have over 20 websites hosted there and trust them with all of my clients.
5:57 am
Knowing how long ago the credentials were stolen would be helpful.
7:15 am
Agreed. The last update on the situation was at 3:53am and no further information has been released.
tim
6:01 am
I am glad your on the ball and protecting everyone.. I was confused by your letter I did not know what "wpengine" was , if you would have said in your email it was a hosting account I would not have gotten so concerned and upset at first..
Since I am not hosted by them then I do not have to worry about it..
Thanks again for your constant diligence.
Bernie6911
6:46 am
Hmm. Interesting. But, doesn't WPE not allow WordFence on their servers? That is one of the things that is keeping me from moving over to them, to be honest. I rely on WF too much to not be able to use it.
7:13 am
You are correct. They currently do not allow Wordfence and several other plugins.
tim
6:49 am
Here's the URL of the topic that provides detailed instructions:
https://wpengine.com/support/infosec/#6
9:49 am
Love the proactive announcement by WPEngine. Thanks for the heads up!
7:46 pm
Yes...pretty nice of Worfence to let everyone know because WPEngine does not allow wordence installations due to conflicts with their own built-in security measures. I have one WPEngine site and the speed is great. Costs more than a regular hosting company but you get better speed and security.
4:33 am
Great to see two companies which don't work in directly together both being pro-active in the announcement, a quick to resolve any issues. I am a recent adopted of WP Engine, and whilst it would be great id there were to allow Wordfence on there servers,
I'm not put off by this, i always judge a service not just on performance but also on support. One area they are let down on is reliance on email to make client notifications especially when there are so many choices in terms of communication methods, something i hope they will address in the near future and for myself making use of IFTT will bridge the gap temporarily.
6:46 am
Thanks for sharing this information. I've alerted my clients who use their service.
1:11 pm
When I saw it first I was a bit afraid and asked myself, for I didn't know: was I a customer of WPEngine? I didn't remember but the name was so familiar to me. In the end it proved I wasn't, I just visited their website some time ago but I didn't created an account with them.
5:14 pm
WP Engine compare to Wordfence who is the best player??
7:32 am
WPEngine is a hosting provider. We make a security plugin you can run on any WordPress site. So we are in different businesses.