Scary Data – Trends in Malware, Phishing, Site Cleaning and Bad Networks
At Wordfence we have great visibility into the size and scale of the threat facing the WordPress community. Our software protects well over a million sites worldwide. This week we thought it would be interesting to provide you with a broader perspective, analyzing some of the information that Google has made available in the Safe Browsing section of their Transparency Report. As we dug into the data we found a number of insights that we think you will benefit from.

Almost Half a Million Malware Sites
The number of Malware sites continues to grow, hitting a new peak of 489,801 in October of 2015. That is up over 160% from the same time the previous year. As we have discussed before, a website that is infected with malware can install malicious software on your computer if you visit it. Attackers use the software to steal sensitive information from you such as credit card information and social security numbers.
As an internet user, the growth in malware sites means that the odds of you accidentally visiting one and becoming infected continue to increase. Google and the other search engines do a decent job of flagging them, but they can’t catch all of them in time to provide complete protection.
As a website owner, it means that attackers are having more success than ever compromising websites. It goes without saying that we think you should take website security seriously.
150% Growth in Phishing Sites in 7 Months
According to Google there are now 293,747 phishing sites on the internet, up from 113,132 in July of last year. This represents growth of over 150% in a mere seven months. A phishing site attempts to trick you into thinking it is legitimate, like your online bank or an online retailer. They then lure you into providing login credentials or other sensitive information. In the Introduction to WordPress Security article in our Learning Center we talk about how attackers are even using phishing tactics to steal WordPress credentials.
This is a significant trend, representing a threat that you should now be much more wary of.
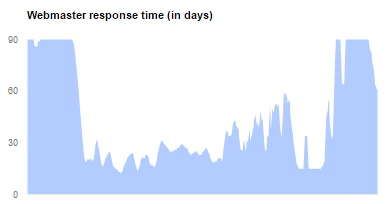
It’s taking webmasters up to 90 days to respond
Google measures how long it takes for webmasters to take action after they have received notice that their site has been compromised. Over the last year, the fastest average webmaster response time reported was 61 days, and for much of the year it was 90 or worse.
Wait, what?
We found this statistic to be absolutely shocking. As we have gotten to know our customers better and better, it has become very clear that their websites matter. In fact, in our recent WordPress Security Survey, 66% of respondents said that a compromised site could affect their income. Based on this, our theory is that the slow response time is not generally driven by apathy, but by a long lag time between infection and discovery. If you aren’t already proactively monitoring your site for compromise we strongly recommend that you spend some time reading our Learning Center article on how to detect a hacked website.
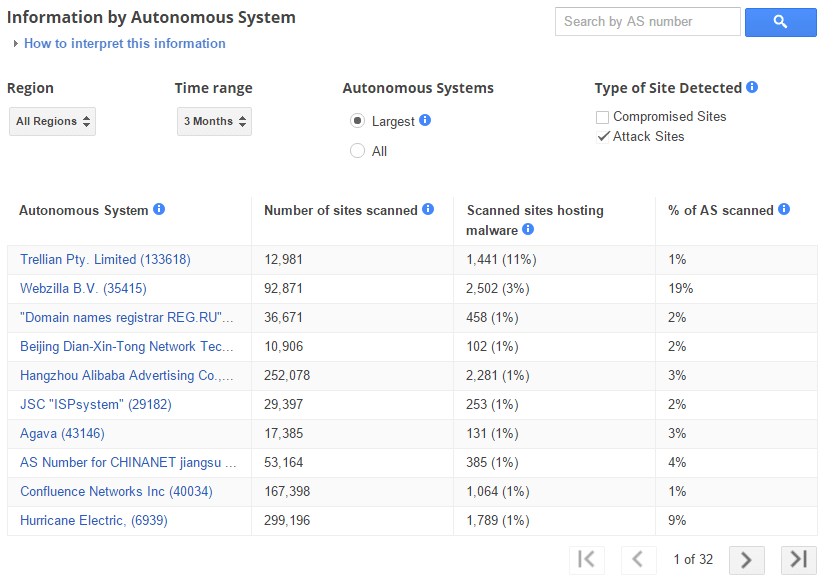
Which neighborhoods to avoid on the internet
Google provides very interesting data about the rate of infection for different Autonomous Systems on the internet. An Autonomous System is a network level designation that represents a pool of IP addresses that are under the control of one or more networks on behalf of a single entity. You can think of it roughly as the group of IP addresses that have been assigned to an ISP. The data is very interesting, and aligns with what we learned in the analysis of brute force attacks we did a few weeks ago.
The thing that jumps out the most to us is the incredibly high penetration of infection on some Autonomous Systems. With infection rates as high 49%, there are areas of the internet that we would strongly encourage you to avoid. If you want to check out what Autonomous System your IP address belongs to, simply enter it into this handy tool. The good news is that the large majority of Autonomous Systems have infection rates of 1% or lower. We hope that Google’s reporting will serve as a call to action for the networks with the biggest problems.
The other thing that jumps out is that this is clearly a global problem. As you page through the list, there are numerous countries spanning the globe represented. This problem is impacting all of us.

On the other side of the coin, we see a similar situation with Attack Sites. While there is a little more concentration in countries like the United States and China, you would still need to circle the globe to visit all of the biggest offenders.
Rising to the Challenge
The team at Wordfence has been hard at work on this problem for years now, and we are really proud of the product we have created and how it has been received by the WordPress community. As evidenced by the insights above, and numerous others from our other blog posts, the scale and complexity of the threat facing website owners continues to grow dramatically. That is why we have continued to invest in our team and our product. We have very exciting news to share with you in April about how we will be making the best security solution for WordPress significantly better. Stay tuned for a big announcement, we can’t wait to share it with you.

Comments
9:21 am
One reason that it's taking so long for webmasters to respond to these problems is that they don't know they're happening.
Google isn't always emailing the owners when it detects a problem. I don't know about you but I can't check the webmaster tools every day for all of my sites
9:08 am
On the subject of webmasters taking a month or more to respond to their site being hacked, it could also be due to factors other than just not noticing the vandalism. At least, that was my experience.
I was hacked late last year and took prompt action. Or such was my intention. In reality, something else occurred.
My ISP at that time not only failed to respond appropriately but inexplicably appeared to actively interfere with my efforts while my infected site was left live and online for weeks. At one point during that frustrating month-long process I went so far as to deliberately crash my site by deleting all pages that I knew were infected, as well as the home page, in order to get the webpage offline yet in response to my trouble ticket the host restored it with all of the malware injection links left intact. Their tech actually told me that everything had been removed and the site was now clean so I requested Google rescan the site to lift the blacklisting. Google soon found the original malware injection site links were ALL still present but now they were accompanied by over a hundred new ones so they wisely preserved the blacklisting blocking my website.
I would suggest my experience might shed some light as to another possible reason why webmasters might seem slow to respond and why a month appears to be common.
During that time period, tech support began taking from 7 up to 12 days to respond to my trouble tickets requesting my site be taken offline due to being infected with malware and their online chat support was replaced with an automated option to "leave a message". It took almost a full month before they complied with my repeated requests to get the site offline and it required more than a month to resolve the problems. It was so bad that I changed my ISP despite still having a paid year of web hosting left.
I have to wonder how many other webmasters might have shared my experience during their first month of attempts to get their websites clean?
9:39 am
Michael,
I encourage you to install wordfence, then install Infinite WP (or the like). You'll get emails when there are problems and you can update your sites with one click. I generally act within 12-24 hours, immediately if the wordfence crew advise me to.
It's much better to act quickly than have to clean malware of your websites.
Pete
6:21 pm
Completely agree with this. Having ability to be informed via email by Wordfence really is a time saver. Respond time can be much quicker to diagnose infected sites. I'm still new to Wordpress environment but WF is among the first plugin I installed (on every installation) and constantly poked on daily basis.
9:51 am
Great, interesting article as always guys. As a digital marketing consultant and digital marketing company owner, we alert clients straight away when we see errors in Webmaster Tools. It's vital for both user security and a businesses' standing with Google that these compromised sites are dealt with as soon as possible and certainly in less time than 61 days!
12:43 pm
I agree with Michael that GWMT can't be checked everyday, but its a good habit to at least check once a month. Also, its is very helpful to have WordFence installed. I get notified when anything is outdated or an attempted login occurs.
Good post WordFence! I always enjoy reading them.
1:55 pm
The actual number of site that are hacked is much greater than these numbers suggest. Hacks whose primary purpose is black hat SEO and hacks with redirects or links to hacker controlled servers. Sites that are obviously hacked but do not present an immediate threat are pretty much ignored by Google.
2:34 pm
Excellent stats very few might be aware of. I always recommend using Wordfence since it solves a lot of problems in one go. Apart from updating the sites, keeping the periodic server backups, check Wordfence notifications, taking actions we run a few tailor made bash scripts which help a lot to keep the sites secure. As far as the GWMT notifications are concerned, we take immediate actions as and when notified since taking prompt actions keep the sites up and running and also save us SEO wise as well.
7:39 pm
I think a lot of the 'US/ Europe' IP addresses are actually proxies used by those outside the country. The attacks I see say 'France' - why would a Frenchman hack an English site? - He's not French.
I have 2 locked down Nginx servers and the only one consistently attacked has Wordpress on it. Time they upped their game. Despite country blocking, med sec and so on - the attacks are still at 200 a day across 15 sites - Bots guessing logins.
Google has a new patent for filtering incoming traffic. Essentially a firewall that checks valid headers, all incoming IP's for actual ip address vs IP address etc. so looking forward to that implementation to kill spam and attacks etc.
Patent granted Dec 2015
11:27 pm
As far as regards Google Search Console (once GWT) you can set an alert via email, so you don't have to check every day ....
Besides this, use all the instruments to secure your site.
90 days to solve a hack is really scary!
3:25 am
Thanks for your articles. Sober and thorough. Where do I find the enire list of all ISP's with infected sites? I can see that the list in your article is only the first page of more than 30 pages.
10:12 am
The data is here: https://www.google.com/transparencyreport/safebrowsing/malware/?hl=en#region=ALL&period=365&size=ALL&compromised&attack&asn=25535&aggregation=RATE&page=8
Quite interesting is that it's only the first few pages that have more than 1% infections/attack sites.
I had to hunt around for it too!
5:12 am
I think that patent is also one to combat referral spam in Google Analytics. It's a major pain at the moment... I'm interested to know why WordFence doesn't give the ability to change the login slug. I assume that's coming?
5:35 pm
We have noticed our sites getting hit regularly in the past year - thanks to the Wordfence alerts we can stay on top of thing to some degree.