Huge Increase in Brute Force Attacks in December and What to Do
Update: We posted a follow-up to this post on Monday December 19th which goes into more detail about the Ukraine IP block where these attacks originate from and we discuss possible Russia involvement.
At Wordfence we constantly monitor the WordPress attack landscape in real-time. Three weeks ago, on November 24th, we started seeing a rise in brute force attacks. As a reminder, a brute force attack is one that tries to guess your username and password to sign into your WordPress website.
In today’s post we show you how attacks have increased during the past 3 weeks and share some data about where attacks are originating from.
First: How to protect yourself from these attacks
Brute force attacks are unsophisticated. They are simple password guessing attacks. A machine will automatically try to sign into your website over and over in the hope that it can guess your password.
If you install the free version of Wordfence, you are automatically protected against brute force attacks. It’s that simple. We also automatically block the worst offenders completely, and we share some information below on who those are.
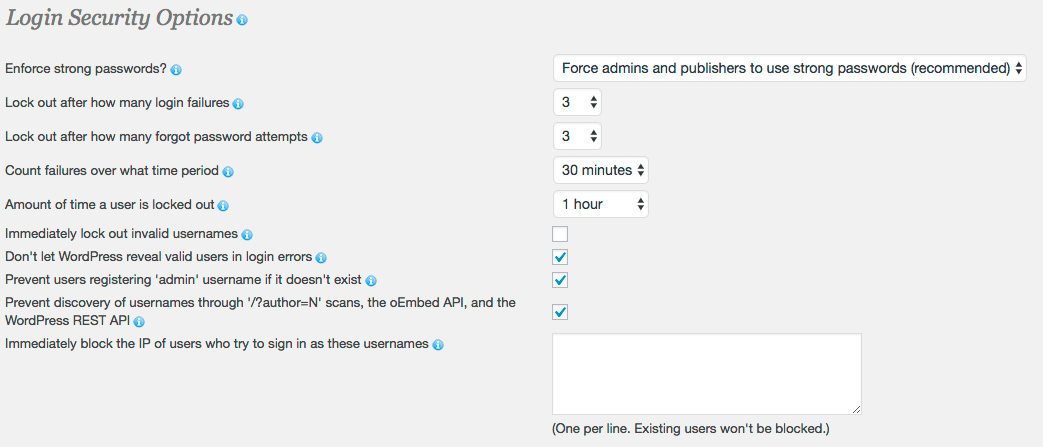
We have a few other really cool options, like preventing username discovery and immediately locking out invalid usernames. All these techniques help protect you against brute force attacks.
Download and install the free version of Wordfence today to get instant protection against brute-force attacks.
A sustained increase in Brute Force WordPress Attacks
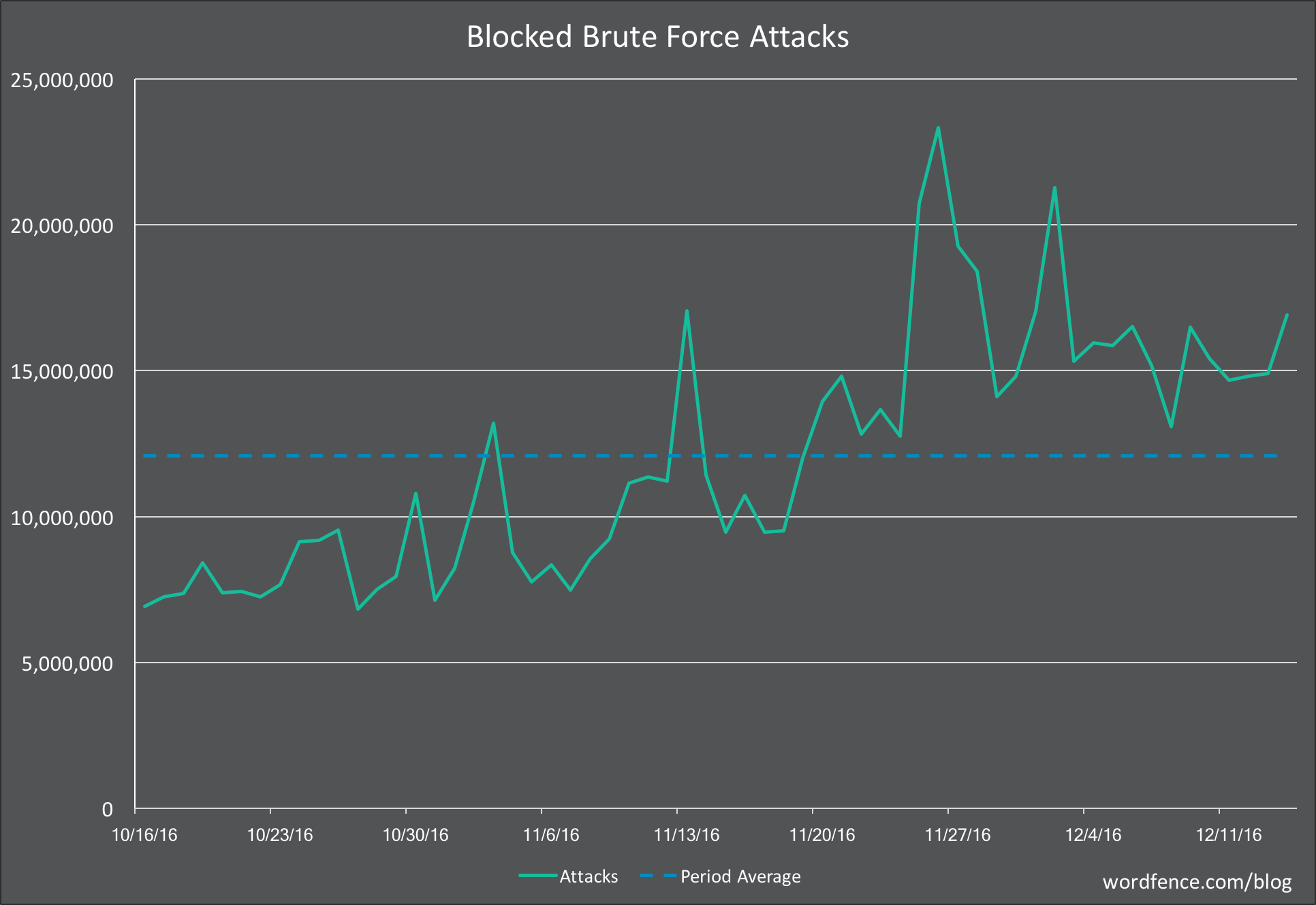
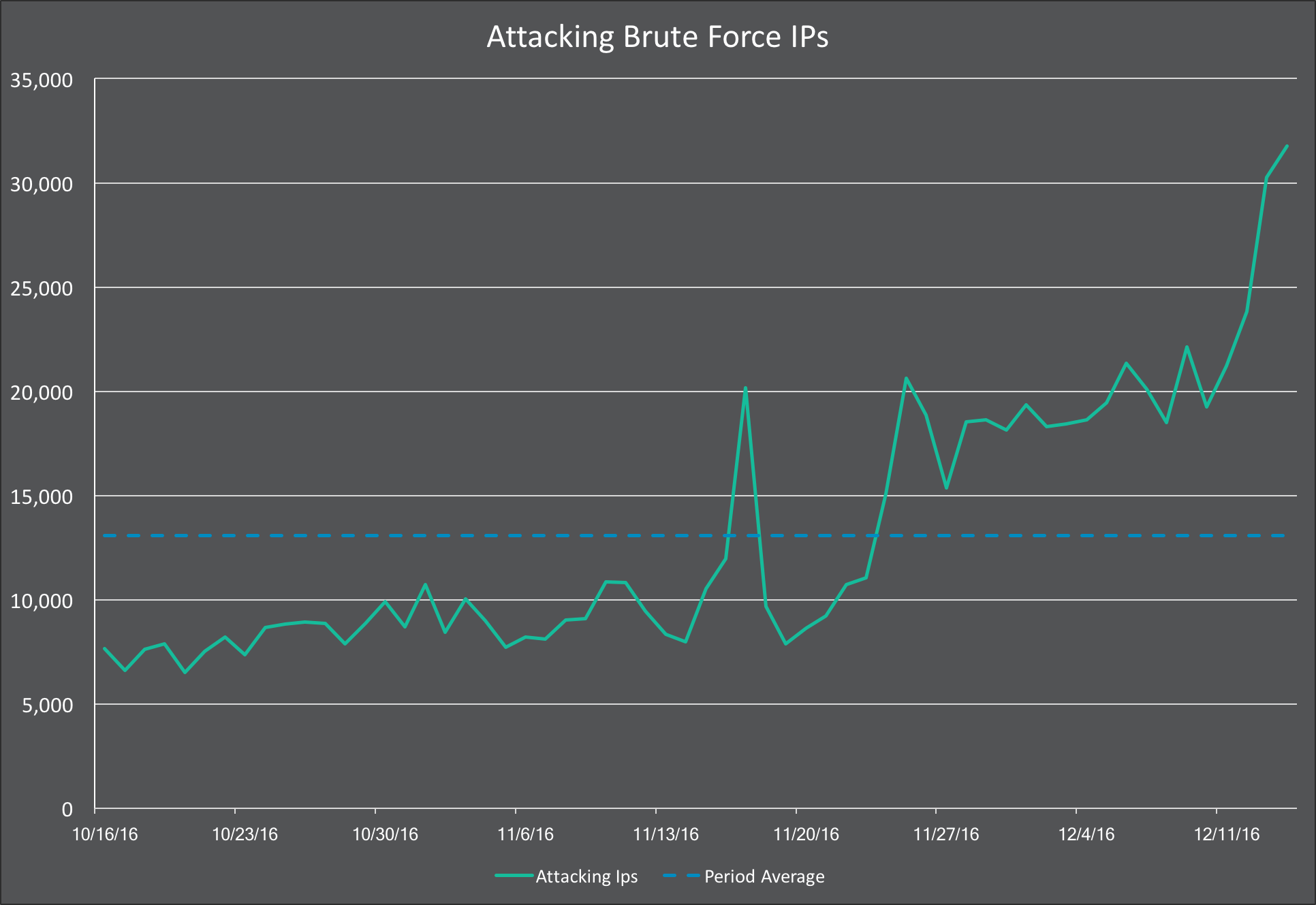
During the past three weeks we have seen the number of sites attacked each day almost double. The dotted blue line indicates the average number of attacked sites for the 60 days shown. The charts below show attack patterns over the past 2 months.
We have observed the number of brute force attacks blocked increase significantly above our 60 day average.
And what most concerns us is that we have seen a rise in unique IP addresses that are attacking WordPress websites per day. This rise started on November 24th and has spiked significantly during the past week.
This has now increased far above our baseline. Usually we see an average of around 13,000 unique IP’s attacking each day. We’re currently seeing over 30,000 unique attacking IPs and this is continuing to increase.
Who is Brute Force Attacking WordPress sites?
The charts above show data for the past two months. We then analyzed attacks during the past 24 hours to see who is currently attacking WordPress sites.
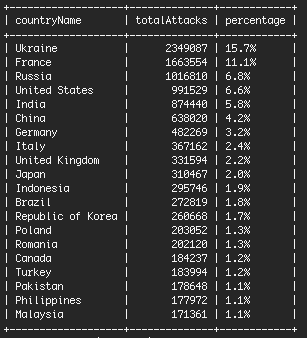
The following table shows the top 20 countries sorted by attacks during the past 24 hours. As you can see, Ukraine is by far the main culprit, responsible for over 15% of total attacks. That is a lot when you consider that the population of Ukraine is only 45 million people.
Most of the attacks come from 8 IP addresses in Ukraine.
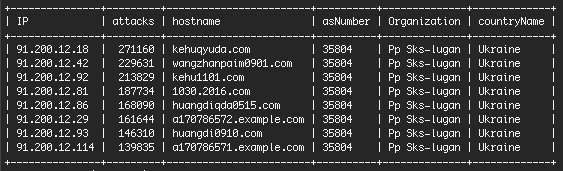
These IPs all belong to the same organization and are on the same network. Doing a Google search on the top IP brings back many reports of abuse around the Internet. They belong to a hosting company in Ukraine called “Pp Sks-lugan“. The servers are a mix. Some aren’t running any services. Others appear to be running Windows IIS web server.
These IPs are using brute force attacks exclusively. They don’t launch any sophisticated attacks. They are hammering away at WordPress sites at a rate of over a quarter million login attempts each, in some cases, during a 24 hour period.
When we add up attacks during the past 24 hours and group by the organization that owns the attacking IP address, you can really see the impact that the Ukrainian host is having.
Keep in mind that as you look at the data below, some organizations like GoDaddy are very large. They actually make up a large percentage of total WordPress sites on the Net. And so before you call out a hosting provider for being ‘insecure’, you should consider their size and that it takes the operations team at each hosting provider some time to respond to a hacked site and take it offline.
We also think the table below illustrates how most attacks originate from specific networks that are relatively obscure.
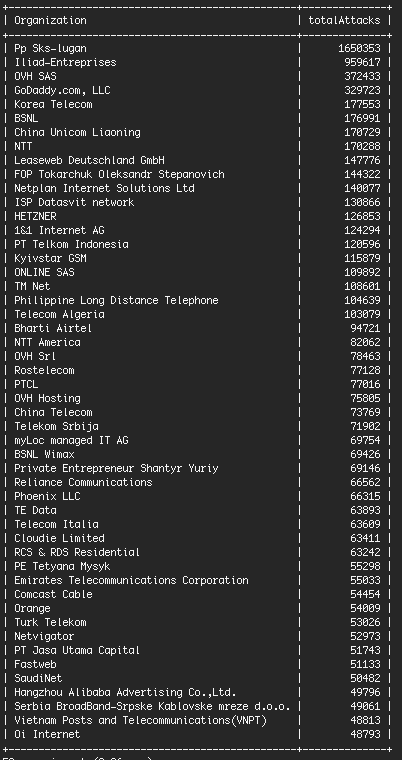
The top hosting provider is a tiny organization you’ve probably never heard of. But they’re head and shoulders above most other companies on this list for the number of attacks that originate from their network.
The second company on the list, “Iliad-Entreprises”, has 8 IP addresses in particular that launched between 50,000 and 210,000 attacks each during the past 24 hours. That is what makes up the bulk of the action on their network.
The difference between the top two networks and the network in third place is dramatic. OVH is a very large hosting provider, but we’re seeing more than 4 times fewer attacks originating from their network than from the #1 Ukrainian host.
Lock it down and stay safe this holiday season
If you run a WordPress site, make sure you lock it down so that you can relax over the holiday season. Brute force attacks are easy to protect against if you have the right tools. I’ve included a screenshot below of the Wordfence Login Security options that give you an idea of the many different ways we stop brute force attacks in their tracks. Click for a larger image.
As always I would love to hear your feedback and comments below and will be around to respond.
Mark Maunder – Wordfence Founder/CEO
Thanks to Matt Rusnak and Dan Moen for their assistance editing this post.


Comments
8:49 am
Great post as always - I would always recommend Wordfence as the very first plugin to be installed on any new WP site being developed, and added to any existing site I come across.
Interesting statistics given the sheer volume of attacks from just a handful of origins!
8:49 am
Very interesting to see these numbers! Keep up the good work.
8:59 am
Great article - and timely. We've been seeing an almost identical ramping up of. Rite force attempts on SMTP services - from pretty much the same geographic locations.
8:59 am
Good looking out, as always, Mark --
We also use the following rate-limit feature on Nginx, if it helps anyone:
`limit_req_zone $binary_remote_addr zone=one:10m rate=1r/s;
limit_req_status 444;`
...combine above with below, or above in `nginx.conf` and below on your server block:
`location = /wp-login.php {
limit_req zone=one burst=1 nodelay;
fastcgi_split_path_info ^(.+\.php)(/.+)$;
fastcgi_pass unix:/run/php/php7.0-fpm.sock;
fastcgi_index index.php;
include fastcgi.conf;
}`
9:00 am
This Ukraine! Why so many attacks from there?? Not only with this case, always!
5:01 pm
It's been that way since Russia started invading Ukraine. So basically Russia is hacking us. Russia has been and always will be our main cyber nemesis. There is an unwritten law in Russia that as long as your targets aren't homegrown you get a pass and can even get brownie points for targeting the US.
9:03 am
This is no surprise. All my blogs have been under attack for weeks. All are running Wordfence and one has Sucuri runnig as well. If the source of these attacks is known, why can't they be shut down?
9:48 am
They are in a wide range of juristictions that have a variety of different laws and in some areas enforcement is unreliable.
Mark.
1:10 pm
Sks-Lugan... the most likely there is only one law - of brutal force and they are good in applying it.
The most likely this comes not from Ukraine, but from Lugansk/Donetsk "republic"
9:03 am
Interesting to see NTT on there is it same as NTT Data the texh services company? Have you informed each of the hosting providers about this?
9:04 am
I have noticed a major increase in attacks already, even against some minor traffic sites I maintain. I've blocked all of the countries outside the US and have blocked out invalid usernames. After I blocked all foreign countries, I immediately noted that the attacks started coming from IP address in the US.
So, Thanks, WordFence, your services are worth every penny it costs for the piece of mind in my viewpoint.
9:04 am
This is just another reason why I have just protected all my client accounts with WordFence Premium!
9:48 am
Thank you for your business!
9:04 am
IPs like "91.200.12.18" are also hammering mail servers using dictionary attacks, they are not brute-forcing WordPress only; I think they are testing every kind of open service they find on a server.
3:50 pm
We noticed the same thing a few days ago with this IP range using brute-force attacks on some of mail servers. I blocked this entire range in our head firewall and then saw this blog post today. Once I blocked these guys out, our brute-force attacks dropped at least 75%.
3:28 am
Hi, I asked more infos about this IP pool, and the answer is that you can block a huge range (91.200.12.0/22):
https://www.spamhaus.org/sbl/query/SBL190623
They're hosting malware/DDoS botnet, spammers etc.
9:05 am
I definitely noticed a spike in brute force attacks for many clients over the last few weeks. I also noticed a lot attempts at root access to the server. For anyone managing a Linux server I'd recommend adding Fail2Ban.
9:06 am
All my Clients have wordfence installed with wordpress and never had their sites hacked.
I also would and do recommend Wordfence , if you dont have it installed on your site get it now.
9:07 am
Thanks for the advice, cyber crime is only going to be on the rise as more and more people around the world do business online.
9:07 am
With my paid WF I see that I can block whole countries. Since no one outside the US or Canada will have any interest in my site, does it make sense for me to block the problem countries you mention above, or even the ones I see reported on my dashboard?
9:50 am
Hi Trisha,
Wordfence does an excellent job without any country blocking enabled. If you want to block countries, I'd suggest only blocking one or two specific culprits that you have a very clear problem with. I don't recommend 'whitelisting' countries, where everyone is blocked by default except a select few. If you do that it's easy to make a mistake and block someone who is on vacation or has no ill intent and wants to visit your site.
Mark.
9:10 am
As an Internet writer, thank you for making my job easier.
9:47 am
You're very welcome Roger!
9:10 am
Very interesting statistics, thank you.
I've noticed 91.200.12.* figuring high in weekly Wordfence reports for many weeks now.
Do you take any proactive action against these kinds of offenders? Is there some sort of authority to contact? Or maybe block them by default for all Wordfence clients?
9:14 am
As a side note,
the magnificent "advanced blocking" feature should help block them manually, by entering
91.200.12.0 - 91.200.12.255 as the ip range.
9:45 am
Good point Tanel.
9:47 am
Yes, they become part of the Wordfence Security Network and we block them across all sites from performing any brute force attacks.
We don't contact the network owner to file an abuse complaint. As I mentioned to another commenter, it would be quite labor intensive for us because we track a lot of attacks and attackers.
Mark.
9:10 am
Had our hosting company block a range of ip's, ukrainien, just as above. Yesterday morning wordfence was sending me alerts for over an hour that this ip was attempting to get into one of our sites.
9:11 am
Thanks for your advice
9:13 am
I've noticed an up-swing in failed login attempts.
Best hint/tip I can give is : audit your user names and incorrect login restrictions.
Keep away from usernames like : 'admin' 'guest' '' 'test' 'owner'
I've had a few attempts every day since November, usually going for 'admin' & 'test' (as well as the others in my list) neither of which exist in my wordpress user list.
That and a very Strick : "auto-block if user doesn't exist" & "one fail and i.p blocked" policy keeps things nice neat for myself.
12:46 pm
Hey Bill, how does that work if you have customers that incorrectly enter their username when trying to log in? I guess it doesn't matter if your site isn't set up that way though.
2:35 pm
I second this. I maintain a large list of the most popular generic usernames and use WordFence to automatically block attempts to sign in with those usernames on all of my sites.
9:14 am
weve seen this for the last 6 months that these countries have been responsible for most attacksbut we noticed that since black friday a huge increase of spam accounts on facebook and twitter also, maybe something for others to keep an eye on as we found even posting a post results in keywords being used to attempt access
9:15 am
Great but very scary information. This is exactly why we have wordfence installed on all of our WordPress sites.
We do however configure it a bit differently than what is shown above. We lock out after 2 failed login attempts and after 1 failed forgotten password attempt. We also count those failures over a day and then lock out for a period of 60 days.
We also immediately block any IP that uses common usernames such as admin, administrator or the site name.
What is your opinion on these settings? Are we going overboard?
I will say that all of our users use a password manager and have very complex passwords (20+ characters combining upper and lower case letters, numbers and characters).
Thanks for keeping us (and the world) informed on these continued attacks.
9:45 am
Hi Ken,
Those settings are on the strict site, but it's not far off what we do on this site. We lock out after 3 fails and you're locked out for 24 hours. That's why we make the settings customizable.
Mark.
9:45 am
PS: You can see our own settings in the screenshot at the bottom of today's post.
9:17 am
Excellent to see these security updates as they become available. Thanks for being there. Happy Christmas and a Great New Year to all of you.
9:19 am
Out of curiousity Mark, why would preventing users registering 'admin' help protect a site? If the site owner hasn't used admin for any log in protocols, and if admin is one of the most popular guesses that a brute force attacker will use, are you not better off leaving that option open to them to hammer away at in the sure knowledge that it doesn't work, rather than eliminating it for them?
9:44 am
It can be used in phishing attacks where a subscriber level user on a WordPress website convinces another user of the same site that they're the site admin. They could fool a user into disclosing sensitive information to them.
Mark.
9:20 am
I install Wordfence as literally my first action on a new site, before I do anything else.
9:43 am
Thanks for the great feedback Dale. It's always great to hear that from a customer.
Mark.
9:20 am
Excellent article - very informative. It's good to name the culprits although their skins are probably so thick that they feel no shame.
9:21 am
Keep up the good work and thanks for keeping our site safe.
9:22 am
I have Word Fence protecting our site and has been great. I'd noticed that our site was getting hit more than usual. I can never figure the advantage but that is just me. Thanks for the information.
9:25 am
Woow, awesome staff.
I really have to thank the team at Wordfence. I have been noticing the figures in my Wordfence dashboard inside my wp site. Its really too much. Thank you for giving us an update and such an insightful writeup. If we got pro with Wordfence, what are some of the exciting features?
9:42 am
Hi Kwema,
The most important thing you get with Wordfence Premium is real-time rule updates for your firewall and real-time scan signature updates for the malware scan. You get many other features like two-factor authentication, but the real-time rule updates are the most important.
What this means is that, as new threats emerge, we release protection within a few hours and your site is updated the moment we release an update.
In the case of malware scan, our site cleaning team are constantly cleaning hacked sites every day. So as we see a new malware appear, we quickly add it to our detection capability and release that in real-time to our Premium users.
Free users have to wait 30 days until they get a firewall rule or scan signature that was released to Premium in real-time.
Mark.
9:26 am
Have you already contacted "noc@lugalink.net" and "abuse@vhoster.net"? If so, what did they told you?
9:39 am
We don't contact abuse contacts ourselves. It would be very labor intensive for us because we track millions of attacks daily.
Mark.
3:30 am
Hi Mark,
I asked more infos about this IP pool, and the answer is that you can block a huge range (91.200.12.0/22):
https://www.spamhaus.org/sbl/query/SBL190623
They're hosting all sort of malware, DDoS botnet, spammers etc. And they don't reply to spam reports.
9:31 am
Glad that I have most of these offenders (countries) blocked, thanks to Wordfence Premium :)
9:31 am
Thank you for providing all these details. I had no idea. My website got hacked late in November and it became a 5-week nightmare. I've studied the subject a bit now, but did not realize the extent of the problem.
Thanks for providing solutions as well. It seems safe now that I have installed a few security plugins, including yours.
However, I still get about 100 brute force attacks a day! Unbelievable what some people like to spend their time doing... and very sad.
11:29 am
Yep, you are right, they are folks out there who has it as a 'hobby' to try and 'take out/compromise' as many sites as they can. This is why a person should have an operational security package (i.e. 'Wordfence') on their site, at site launch. A security barrier is mandatory these days, and it is not an item to take for granted. You need to make reviews of what is happening, so that if necessary, you can crank up options available in your security package. Take the opportunity to go through all of the options of the Wordfence package offerings, to understand what is available to you for 'tweaking', if necessary.
9:35 am
Thanks for the educational post.
I recently started using Wordfence on all my sites and I'm grateful for the security it provides.
9:35 am
I see the same attacker, not just on WordPress sites, but trying to guess ftp passwords: from Ukraine, Russia, Bulgarien, Estland, Slovakia, and I see lots of attacks using the same providers.
This attack is going on since november on my customers machines too. The attackers use their IPs two times only, and they come up with some 100 new IPs every day. Just during the last days the attacks are getting slower, I guess as we block large blocks of IPs on port 21 and 22.
On every machine we see that they got real names from companies, even though these names aren't published on my customers webpages, but none of them has an ftp account.
'Dress warm' is what we say here in Germany
Ulrike
9:41 am
After reading your article, I watched in real time as a site in Zagreb, Croatia tried to access my wp-login page twice. Thank you so very much for the protection you afford!
9:42 am
We have noticed the same increase across our servers. Our mod_sec rules automatically block and ban these brute force attacks on Wordpress and a bunch of other cms and forums.
I receive a "hit list" summary daily which i review, and that list has grown substantially over the past 2 weeks. Most definitely this is on the rise,
9:47 am
Thanks for the great posts. I have a number of Wordpress sites, all of them enjoying Wordfence protection. I actually had times with a lot more attacks, although I use stricter lockout settings after failed attempts. Thanks for posting, Jeep going
9:54 am
I noticed a huge increase of attacks particularly from Ukraine. Wordfence is doing absolutely great job locking out the attackers. However, I am wondering why is it that when Wordfence knows the network of these attackers, why would they not block them permanently. I spend a lot of time deleting the emails from Wordfence exposing these attacks. It would save me a great deal of time if Wordfence blocks these attacks permanently.
I would really appreciate it.
9:55 am
Thanks for the post.
Yes, we have seen an increase in brute force attacks - around 1200 for over 2 days only. We use hide my wordpress plugin from envato combined with wordfence premium and cleantalk, and they greatly help. There are times wordfence is not able to stop specific IP's. It shows on my system that IP has tried to attempt BF but WF has not caught it nor can it block the IP. I then have to block it at the apache level? Any suggestions on why this is the case?
9:56 am
I've been seeing this with my sites. I had to restrict access for one site to the "US only" it was getting so bad. Thank God for WordFence!
9:56 am
Well , the brute force login attack started almost a month ago, at least a month ago I've started to notice and my option was to manually block all attempts ... I've also notice a pattern, the username used seams to be most of the time "test" --- even if I've added the username as trigger for automatically block in the Options nothing happen ... I've also use Pike Firewall (because wordfence doesn't show the trigger) and it looks like this
POST: log=test, pwd=skater, wp-submit=Log In, testcookie=1
COOKIE: wordpress_test_cookie=WP Cookie check, wfvt_2179047538=5853fe363fc39, _geo_ip={"ip":"61.0.16.102","country_code":"IN","country_name":"India","region_code":"UP","region_name":"Uttar Pradesh","city":"Kanpur","zip_code":"208015","time_zone":"Asia/Kolkata","latitude":26.4667,"longitude":80.35,"metro_code":0}
Yes a bit messy but helpful never the less.
I like using Wordfence it is reliable but sometimes seems that firewall has some bricks missing.
10:09 am
Mark, Thank you! You all are worthy of rave applause!!
I noticed the increase you speak about here as well, and have taken precautions against it. My only question is what may be motivating the increase?
Bluehost just issued a notice that they are ramping up security as well.
Obviously Word Press is a target. I would like to know what the Word Press developers are doing to fortify their product and its design against such an onslaught.
As always, you guys are the BEST! Thank you for all you do. Your service is outstanding!
10:17 am
I remember before when my website was hosted on iPage even though Wordfence blocked a lot (I put block immediately when someone signs in with unused user account), the website continued to slow down due to all the requests.
What I did was that I used a plugin to rename wp-login to something else and put in the htaccess that when wp-login is accessed it should send out a 403 header.
Once I did this, my website immediately went from slow to lightning fast, so to all people having problem with site loading speed, giva a bit more of resources to Wordfence and hide your login page (if people don't need to login to your website as subscriber, that is)
Another tip is to use Clef as sign in process, no one can brute force your password as you will no longer have a password! :) Though POST requests will still happen with Clef, which will be filtered by Wordfence, they will be unsuccessful as you don't use a password anymore.
12:53 am
I totally agree. Changing our login page has totally avoided the attacks we were getting. This is the one feature that I would like to see added to Wordfence.
10:19 am
Thank you!
10:22 am
I run three WordPress sites and wouldn't consider running them without Wordfence. I watch the Live Traffic in the plugin and regularly watch the attempts to hack my sites and usually block countries who will never have any of my customers and who have a high number of hackers. The countries listed in this article are the same ones I've seen on all my sites.
I wanted to mention the other steps I use to lock down my sites so that I NEVER worry about brute force attacks. First, no one but administrators log in to my sites. Second, my settings in Wordfence are very tight in terms of failed logins and once failed the user who failed to login will need to return tomorrow to try their pathetic few attempts. If I'm the one who fails to login by mistake, I can go through CPanel and follow steps to disable Wordfence for a few seconds until I login and then reset security. That has happened once in 8 months. So, with that basis, here's what else I do.
First of course, I use a free SAN SSL cert to login to the site and force SSL logins in my .htaccess file. Any Internet user can view the site with or without using SSL. Second, I use random user IDs for my admin accounts, like pHog_h0rnsammiE32 and 12-15 randomly generated passwords for those accounts. Third, in CPanel, I password protect the wp-admin folder with 15-25 character usernames (that make less sense than the one above) and equally complex and random passwords. These change every 30-60 days depending on what I see in Wordfence Live Traffic. I can see hackers banging the site for 5-9 tries then moving on or trying to upload files, search for compromised plugins, etc. It makes me laugh before I go to bed and sleep like a baby.
I have all my usernames and passwords stored on an encrypted folder on a USB drive and cut and paste all the login information as I login to each site. Once logged in, I clear the clipboard on my local machine in the event I end up on a site that tries to copy information from it. Is all this a pain in the a**? Sure it is, but I've had to rebuild two sites after two other security vendors failed to protect it and it's much easier than doing that. I trust Wordfence and my efforts to prevent ever having to rebuild another one.
When I create a site for paid members in several months for knockoutresume.com it will be a sub-domain and not host a blog or anything other non-commercial. It will include only products and service purchases work. Any completed work files for users to view and download will also be on that site or another sub-domain that customers can login into but not upload or save any information on.
Of all my 'tricks' I'd most recommend password protecting the wp-admin folder, if your site and business allows it. Also, extend out your time for how long failed login users can try again. Make them email you to reset their password, if that's practical for you.
10:37 am
Would you be willing to publish the list of hosting providers who are the TARGETS of the most attacks as well?
I realize the more wordpress sites they host the more likely they are to be attacked so i'd imagine Godaddy, Rackspace, and Hostgator might be at the top but curious to see if someome like WPEngine or other companies get targeted significantly less. Maybe you can assign so
E sort of weighting based on number of sites they host to get to # hack attempts per 1000 sites or something. Thibk this would be very valuable for all of us.
10:51 am
Hi Mark,
This may seem like a silly question but if we change the wp-admin url to something different - would we still feel the effects of the brute force attacks on wp-login.php? I'm debating on if I should make this change on all my sites / any disadvantages? Your advise would be helpful.
Thanks in advance!
10:57 am
Have you supplied this info to the FBI to where they can shut down these attacks from getting through? Just a thought that would help us all as they mostly seem to be coming from just a few sources. Thanks, Russ
10:59 am
As usual, you guys are doing fantastic on staying on top of the folks attempting to compromise internet security! For myself, I have all countries, except for the U.S., blocked. I have seen a spike in Ukraine activity recently. I had previously observed that over 95% of the connection attempts coming from over-seas had been people attempting to compromise my site. The some of the top folks being China, Russia, Ukraine, Germany, Algeria, & Poland. On blocking those top folks, then then switched to other countries, such as Mexico, Philippines, Turkey, and many others. I then blocked all, and noticed another tactic, they switched to U.S. sites. Some of the top offenders coming from Kansas, Washington D.C., Texas, and Los Angeles, among others. Some even started trying to use 'Google-Proxy'.
For scripts that the folks attempt to use, coming from overseas, I put those into the Wordfence 'options' box, to immediately block anyone using that script. For the folks coming from overseas, they are blocked by the Wordfence 'country' blocking. My concern being that I do not wish them to switch to U.S. sites, which are not blocked, and continue attempting to use the previously shown scripts. I keep track of those scripts in a separate file that I keep, which has kept growing!
Wordfence has made this possible, and preventable, by providing the script blocking, as part of the 'options' package. Thanks for that!
11:04 am
Thank you Mark for the post and your good work. Wordfence is just amazing.
I've been experiencing attacks since june this year. The most severe attack I had on my website was on the 1st of July, literally 100+ login attempts per minute. Wordfence was firing up alert emails like crazy. It was consuming the whole bandwidth and my website was unaccessible for a couple of hours. I immediately called Godaddy to see what is going on, and what they have to say, but they simply had nothing. Anyway, after a couple of hours the big attack stopped, and bandwidth and site went back to normal. Though I still receive the alert e-mails - a few every day. I included a code in the .htaccess file and limited the IPs that can access the login page to just one - mine, and redirect everyone else to home page, but no result. Why is this happening? I have tried with many different devices and from different locations and the code works perfectly, but the login attempts continue. What is your opinion on the matter? Any suggestions?
Thanks
11:35 am
Thank you so much. I changed the settings that you recommended.
May I ask 2 questions?
1) How often does brute force actually get through?
2) Is a captcha on a log in page, helpful (I have a math captcha)?
Thank you for hard work. You certainly are amazing pioneers of the internet. I am glad I found you!
Thanks Mary
11:36 am
Thank you for this. I find it very interesting.
My setting lock you out for 48 hours after three fails. Was 72 hours but I backed it down a bit. And using "admin" as a username getting you tossed immediately.
11:38 am
I add 3 rules to every Wordfence install I do.
In Advanced Blocking I add:
User-Agent (browser) that matches:
Mozilla/5.0 (Windows NT 6.1; WOW64; rv:40.0) Gecko/20100101 Firefox/40.1
Mechanize*
Mozilla/5.0 (Windows NT 6.0; rv:34.0) Gecko/20100101 Firefox/34.0
just add a note "hacker" or some such
This won't stop everything but it will drastically reduce the attempts @ wp-login.php and xlmrpc.php
Good luck!
11:40 am
I have both Wordfence and, for the past week, the 6G Firewall on my site. Nothing's been showing up in my Wordfence reports lately. I can have peace of mind and not worry about these brute force attacks. :)
12:01 pm
Hi Mark,
Thanks for the good info and the Wordfence plugin. Both are great tools. I am a premium subscriber and feel it's well worth it. Unfortunately I've been seeing this trend ... living this trend. I audit my live traffic logs nightly and kick attackers off. I have been spending more time and trouble on it and it's very frustrating.
I take a much more aggressive stance than just letting the automation handle things, although the automation is a very powerful ally. In my diary of last night's audit, I counted 32 separate attacks. I'm afraid I do whitelist countries and block all but a few. It's subjective and sort of depends on how many legit requests I'm getting versus the number of attacks from a place. Of those 32 attempted attacks, 24 were automatically blocked by country blocking. I do see a few legitimate requests from some of the same countries, which unfortunately will also be blocked. The other 8 were not blocked by country blocking. On my system though, those (if they're brute force) are almost always blocked immediately since I have xmlrpc.php as a banned url. So, they're actually blocked immediately without ever getting a chance to try logging in. Almost all these attacks start by trying to hit xmlrpc. Those IP's are blocked out for a day.
I go still further. For the IP's that are not being blocked by country blocking, I go and ban the IP's permanently. My thought is that they've already demonstrated themselves to be malicious. Since I'm the only editor, ANY login attempt but mine is, by definition, malicious. Even if they cannot get in with a login attack, they might try other things like plugin or setup attacks that might work. So, I just kick them off. If they haven't tried to access the site in 3 months or so, I might unblock the IP if I get around to it.
I should note that, with the settings you posted in the picture above, the bad guy can try 3 passwords per hour continuously. Particularly if they're in a botnet and sharing data, they could accumulate a database of 2160 failed passwords per site per month per attack bot. I say why let them. I will also acknowledge that you said in a comment that you guys block them for a day, as I do. This reduces their chances dramatically. My rule is, though, if your provably try to attack my site ONCE, you're gone.
In a prior interaction with your tech support people, one suggested I might write a review of Wordfence. I eventually did write a favorable review combined with a blog post on securing your WordPress site and posted it on the WordPress site as well as a slightly larger version on my own blog. Your readers might find it interesting. It's at this address. Your tech support people have already seen it.
https://techstarship.com/2016/12/09/how-to-start-securing-your-wordpress-site/
Here are the major tips, in my opinion, related to this discussion. Options settings may very by site and preference.
- Get the premium subscription. You get the live threat feed and valuable additional features.
- Use a long, 50 character plus, login password. You'll have to use a password manager to track it.
- Turn on two factor authentication with Google Authenticator or similar, not cell phone text messages. This allows you to add a changing 6 digit code to each login password.
- Monitor your live traffic logs to see what's hitting your site.
- Turn on country blocking and block those where you think you're getting too many attacks versus legitimate queries. If would be REALLY nice to be able to choose, per country, whether to block logins only or block your whole site from them.
Note that Wordfence itself has a password audit function with a dictionary of 260 million known passwords. If they have the dictionary, you can bet the bad guys do too. Do NOT use a simple password, any word in a dictionary, any common phrase in a dictionary, any common phrase in a book or movie, etc.
Thanks again for the great product. Hope this info is helpful.
Ron
1:29 pm
Excellent post, as usual.
Mix this attemps increase with the horrible bug on new WP4.7 RestAPI (anyone could take the full user list with a plain public url -example.com/wp-json/wp/v2/users) and it will turn out a problematic Christmas time for many admins out there. :(
12:02 pm
I highly recommend Wordfence Premium. I only market in the US because of our business, so the country blocking is enabled for everywhere except the US.
I had the free version of Wordfence, which was good, but my site was getting hit a lot and I was getting a lot of warnings from Wordfence about attempted logins. Most were from the Ukraine and a few others. Once I blocked the countries, it was like magic. No more attacks. I have it on both of my sites and you should too!
12:33 pm
Many of my sites saw large increases via brute force attacks. Thanks WordFense for an excellent product.
1:09 pm
Hi Mark,
Thanks for the great work.. In your response to Ken you said "We lock out after 3 fails and you're locked out for 24 hours." But the screen shot of your settings shows locked out for an hour. Is this a different setting I need to change or just a mistake? Thanks in advance for your help.
All the best,
Ted
3:32 pm
Sorry, my mistake. The screenshot shows our current settings. I misspoke.
1:22 pm
Fail2Ban, Wordfence and Cloudflare. So far so good. I've not been noticeably affected by any kind of attack in over a year. Prior to that some of the attacks would slow my sites down to a crawl.
1:27 pm
I run 100+ sites for myself and clients and all have WF of course but I have also closed the FTP port and outsourced all mail to Mailgun (from the DNS) as I think it is more secure for them to deal with the mail attacks.
We still get 2000 hits a day on a site but the only back door is SSH with a 32 character password and keys.
No issues for 18 months - Touch wood!
With WordFence on the front door and every other port closed - Works well.
12:24 pm
Hi Graham
This is probably a noob question!
But I was wondering, if you've closed the FTP port, then do you upload/download to/from your server?
Best Regards.
2:02 pm
I got so p***ed off with Ukraine a couple of months ago I just blocked the country entirely.
On another site I have I've recently noticed a large number of attempts to login using the name 'test', usually followed by 8 blocked tries.
Also had a large increase in SQL injection attempts.
2:06 pm
Aaaand here's another from just now...
Győr, Hungary
IP: 94.21.218.149 [unlock]
Reason: Used an invalid username 'test' to try to sign in.
Hostname: 94-21-218-149.pool.digikabel.hu
Last blocked attempt to sign-in or use the forgot password form was 16/12/2016 16:45:09 (5 hours 19 mins ago).
8 attempts have been blocked
Will be unlocked in 18 hours 40 mins
2:22 pm
sudo iptables -I INPUT -j DROP -s 91.200.12.1/24
3:39 pm
Oh hi Steven, I approved your comment and then just realized it was you. Welcome to our blog!! Yup, that would definitely drop all traffic from their subnet at the OS level for Linux.
FYI @sterndata is one of the forum moderators on the wordpress.org forums and helps us out with forum issues from time to time. (Which we very much appreciate!!) You can find his own site at https://www.sterndata.com/.
Best regards,
Mark.
9:18 am
Hi, you can drop much more than the /24 :-)
91.200.12.0/22:
https://www.spamhaus.org/sbl/query/SBL190623
Apparently they only host C&C servers, botnet, scammers, malware
2:41 pm
Great article. I've been monitoring this raise in brute force attacks against one of my client's websites for the past week and was getting concerned that his site may have been singled out. Looks like this is all part of a larger issue from what appears to be a pair of criminal organizations. I'll use this info and lock down my client's site from the offending IPs.
3:57 pm
Thanks for your blog - it explains all the notifications that have gone on for us and our clients over the last few weeks. We always add Wordfence to our clients websites, we think it's a vital part of our setup and security. You do an amazing job informing us and protecting us. Keep up the great work!
4:55 pm
Thanks for this article. I tried to manually enter site addresses of top brute force websites into Wordfence. Kept getting message that I needed to enter a valid IP address - i.e not recognizing the IP addresses listed above. How do I target blocking of these websites? Thanks,
5:40 pm
Thank you for being there and protecting the web.
9:34 pm
I am using Wordfence plugin so I'm always feel free to all atackers thanks share all information to us
1:41 am
Thank you for your great protection service. I can't believe how full my inbox has been over the last while with notifications of all the locked out attempts. Thanks again. :-D
4:43 am
Those Ukranian IP addresses are familiar to me. They were all over my server logs registering fake users on my site. The large number of bounced "welcome" emails got attention.
One point your article didn't mention about brute force attacks is that they don't just have to get the right password - the hacker also needs the right username. Practically all brute force attacks hitting my servers target common usernames such as "Admin". It there is no user called "Admin" then they can never guess the correct password - there isn't a correct password.
This behaviour always struck me as odd. The usernames on my site are no secret. Why don't they crawl my site and harvest valid usernames before and then brute force with valid names.
I'm sure some hacker has thought of this, they just aren't targeting me yet. To combat this potential problem, I suggest people post with a username that doesn't have full admin privileges, thus keeping the username with admin rights private and secret. Effectively create a sock-puppet for yourself on your own site to hide the admin identity.
4:48 am
You have just given me an answer to my questionning about these numerous brutal attacks that I have observed these last few days. But we don't know why suddenly there are all those attacks.
thank you for all the good work you do
8:29 am
Mark - where can we see the Brute attacks in Wordfence? I know in a previous version I was able to see the countries and IPs trying to guess my username and password, but it has since moved and I can't locate it.
Thanks for keeping us safe!
9:33 pm
What I have done to increase the security and block brute force attacks is set the block period to a week to a month, depending on the frequency of hits on the website. If there are enough attempts in a few days, I start adding IP ranges.
With a premium WordFence account, I start blocking countries, which locks them out completely. Since the WordPress websites I monitor belong to clients whose businesses are only local and do not depend on selling outside the local city with the website, I block these other countries in WordFence since anyone from the Ukraine does not really need to see the website.
11:03 am
Hey Mark. I'm wondering is this an overall attack on all websites or is this an organized effort against WP sites because WP has a reputation for being easily hackable by real black hat people?
There are a couple of plug-ins that work to remove signs of all things WP.
For those of us that can't afford the pro version and get country blocking would it be valuable to install one of those plugins to remove the "enticement" if you will?
Or do they cause more problems than they're worth?
I want to thank you for caring enough to provide Brute Force attack protection for free. Most if not all of the other "security" plug-ins require their pro version for brute force attack. I can't begin to tell you how much I appreciate your free plug-in. I would never think of using any other plugin on my own site let alone a client's site.
3:25 pm
Hackers go after the most easy targets. WP is an easy target and is 27% of the web. So that's why WP sites get attacked.
No, removing your login page makes it confusing for your users and can break your application. Wordfence is a super high performance way to stop them from breaking in via brute force. You'll still see the attacks in your logs, which I think is what frustrates some people and makes them want to hide their login page. But it doesn't matter - they won't be able to break in anymore.
Mark.
7:33 am
Thank you for the article.
I, however, found a strange brute force attack on my firewall logs.
Why would a Googlebot, IP's 66.249.79.81 and 66.249.79.88, do an user enumeration scan on a website?
Regards
8:40 pm
Not sure whether it's relevant but some of the hostname of the 8 Ukraine IP addresses can be seen as romanised Mandarin (Hanyu Pinyin). E.g. kehuqyuda == 客户求答 == requesting client's response, huangdi == 皇帝 == king and wangzhanpaim[ai] == 网站拍卖 == website auction.
2:27 pm
I get a lot of bot traffic from China on port 22. Maybe they are now using this Ukrainian provider to run HTTP bots?
Or some group is pretending to be Chinese by using these hostnames?
1:02 pm
Hey Guys,
Hey Mark,
Each month I do a roundup of the best web design, security, and WordPress content from around the web, and I wanted to let you know that I included your post in the December edition. Links is in my bio. Thanks for the insightful post. I was happy to share it with our readers.
Rachel
9:37 am
Thanks Rachel. That's awesome.
Mark.
9:44 am
@MarkMaunder or @WordFence
I was wondering if I reply to a comment on this post, does the OP get an email notification to say "someone replied" or does it simply rely on them randomly revisiting the post?
Best Regards
10:19 am
It's whatever the default is for WP, so I think no email. We don't have an email plugin installed that does that.
1:18 pm
Hi Mark
Thanks for replying!
Can you see there is an opportunity here to increase participation and debate?
Best Regards
3:38 pm
I do. :-) Thanks for suggesting. Will see if I can get this implemented some time soon.
Mark.
5:50 am
Thanks for the educational post.
I recently started using Wordfence on all my sites and I'm grateful for the security it provides.www.mindonsearch.com