9 WordPress Plugins Targeted in Coordinated 4.5-Year Spam Campaign
 On Tuesday last week we published a post that described how someone had released an update to the Display Widgets plugin which contained a backdoor that allowed them to publish content to any site using the plugin. We also described how they exploited that backdoor to publish spam.
On Tuesday last week we published a post that described how someone had released an update to the Display Widgets plugin which contained a backdoor that allowed them to publish content to any site using the plugin. We also described how they exploited that backdoor to publish spam.
We then wrote a follow-up piece which we published on Wednesday identifying the person who modified Display Widgets as Mason Soiza.
In today’s post, we are publishing research showing a coordinated effort by the same spammer that targeted WordPress plugins over a 4.5-year period. In some cases, site owners opted in to a vague agreement that didn’t make it clear that their sites would be serving spam; in other cases, plugins were simply “backdoored” to allow posting without a site owner’s permission.
The content served from the ad network included ads for payday loans and escort services in the UK. The activity started in 2013 and ended this month. All nine plugins discussed today are linked to the same malicious actor, either through a financial trail or through the ad-serving domains used which share IP addresses.
Which Plugins Were Targeted And Their Current Status
We now have evidence that, in addition to the Display Widgets plugin, eight other plugins have been affected by spam in the past and all are linked in some way. These incidents range from May 2013 to September 2017.
In four cases we have also been able to uncover financial transactions linked to Mason Soiza, either directly or indirectly. In other cases, we have no transaction, but we share the data we have which helps establish attribution.
It is important to note that all plugins listed here no longer have the ability to inject spam into websites. They are either safe, or in two cases have been removed from the WordPress plugin repository.
Here is the list of plugins we discuss today and their current status. When we list a plugin as “safe,” it means the plugin does not currently include any spam code that we are aware of.
- 404 to 301: Safe
- Display Widgets Plugin: Safe, but no longer maintained. Use Jetpack’s Widget Visibility Module instead.
- WP Slimstat: Safe
- WP Maintenance Mode: Safe
- Menu Image: Safe
- NewStatPress: Safe
- Financial Calculator Plugin: Safe. Never included malicious code, but Soiza did have access for some time this year.
- Weptile Image: Removed from repository
- No Comment: Removed from repository
Some plugin authors spoke with me anonymously for this post, but most went on the record. My thanks to all authors who helped us compile this data, because they have done the WordPress community a service in helping us understand the impact of these spam networks and who they belong to.
Special thanks to the following plugin authors:
- Display Widgets original author Steph Wells. We spoke via Skype voice and IM. She opened the floodgates.
- 404 to 301 plugin author Joel James. We spoke via Skype IM.
- WP Slimstat author who goes by the alias Jason Crouse. We spoke on the phone.
- WP Maintenance Mode developer George and current owner Andrian. We chatted via email.
- Menu Image plugin developer Alex. We chatted via email.
- Financial Calculator plugin author Ciprian Popescu. We chatted via LinkedIn.
Supply Chain Attacks and Avoiding Bad Partners
What we are describing here today and in our previous posts is known as a supply chain attack. A few examples of supply chain attacks are:
- A hacker breaks into a software company and infects its code with malware, which then gets distributed via the “supply chain” to that company’s customers.
- A developer’s account is compromised and the hacker uses the account to release malicious code to customers.
I have managed to verify that in most of these cases a malicious actor convinced a developer or company to add their code, usually through a financial arrangement, to a WordPress plugin. The malicious actor then uses that gateway to inject spam into customer websites.
As developers, we have a giant target painted on our backs. We are constantly releasing code to customers, and if someone can inject their malicious code into our software, they can infect thousands or even millions of customers at once, rather than just a few at a time. It is very important for us to guard our login credentials and code and important for us to choose our partners wisely.
One could argue that the plugin authors should have been more careful about who they partnered with. I think that is 20/20 hindsight because most partnerships require trust at some point in the relationship. If you put Google ads on your website, you trust Google won’t display offensive content. If another ad network pays you to include their code that displays their ads, you trust them not to include spam or malicious content. In this case, the trust was broken, and in some cases customers paid the price.
My hope in publishing this story, and through the collaboration of these plugin authors who have kindly come forward, spoken up and shared their story, is that we as a community will learn how to avoid bad partnerships and how to form partnerships that do work.
The rest of this post goes into detail about each plugin that we analyzed, how it is linked to the spammer we have been tracking and which versions were affected over what time frame.
Display Widgets Plugin: An Update
We wrote about Display Widgets in detail last week so I am going to summarize the status here and provide an update from the WP plugin team.
I chatted with original plugin author Stephanie Wells via Skype voice and IM. She sold the plugin to Soiza on May 19, 2017, and we’ve confirmed the transaction which came from pp@linkrocket.net.
On June 30, 2017, a backdoor that allowed remote unauthenticated content updates was added to the plugin and remained there until the plugin was removed from the repository on September 8, 2017. The affected versions are version 2.6.1 to version 2.6.3.
The domains used to serve spam were geoip2.io and stopspam.io. The WordPress.org plugin team have removed the historical versions that contained malicious code from the WP repository by the plugin team.
The WordPress.org plugin team have removed the offending code from the latest version of the Display Widgets plugin and incremented the version number so that sites can update to the clean code. I chatted with Otto, one of the plugin repository maintainers, who had this to say on WordPress Slack:
“Version 2.7 is identical to the 2.05 version, codewise. This was done to remove the offending code from the plugin and to help eliminate it from sites that had updated it to the 2.6 series. The plugin is now closed and will receive no more updates. We recommend all users find an alternative plugin for their needs. Given what the intended functionality of the plugin is, I recommend using the Widget Visibility option in Jetpack instead.”
You can find out more about Jetpack’s Widget Visibility module on this page.
404 to 301 Plugin
We received data that Soiza was also involved in 404 to 301 and so we reached out to the author.
We previously wrote about 404 to 301 distributing spam in August of last year. We also did a follow-up post with more technical detail and to counter criticism we received.
I chatted with Joel James, the author of 404 to 301, for this post. He was kind enough to share transaction details with me. Based on a PayPal transaction dated May 9, 2016 from pp@linkrocket.net using Soiza’s name, Soiza also appears to be the perpetrator in this case.
404 to 301 included Soiza’s code to distribute spam to websites from June 1, 2016 until July 12, 2016. The affected versions are 2.2.0 to 2.2.8.
The domain used to fetch spam and inject it into the plugin was wpcdn.io. You can find the code here if you search for the domain.
The plugin injected spam content onto sites, including a domain for a UK-based escort service which we verified belongs to Soiza in the Display Widgets follow-up post.
The plugin asked users to agree to terms before injecting their content with spam, but the terms were lengthy and the ‘spam’ clause appeared right at the end.
Joel James now controls the code to this plugin and has confirmed that the plugin is now clean. As a reminder, this happened over a year ago. At this point I have no hesitation in recommending that you use the 404 to 301 plugin.
WP Slimstat Plugin
We also received data that Soiza was involved with WP Slimstat. I chatted with the author of WP Slimstat on the phone. He goes by the alias Jason Crouse, and would prefer to remain anonymous. He was kind enough to provide all of the data we requested.
He received a PayPal transaction dated November 22, 2015 from email jj@linkrocket.net and name “Garri Kiekbusch.” The email uses the same domain as two other emails that we have established belong to Soiza, but the transaction used a different name. This email was also displayed on an archived linkrocket.net home page along with the other two. The name may be a business partner or an alias.
From October 22, 2013 until August 10, 2016 (2 years 10 months), WP Slimstat had code in it that is very similar to Soiza’s spam code. That period includes versions 3.4 to version 4.3.7.
The domains used for Slimstat were wordpress.cloudapp.net, then wpcdn.io and later api.wp-stats.io. You can find a code sample on this page for 4.3.7.
It’s important to note that wordpress.cloudapp.net and wpcdn.io share the same IP address at the time of writing. api.wp-stats.io historically also shared that IP address. This links the three domains and we will refer to this later in the post.
Early versions of Slimstat that included Soiza’s code included a checkbox that you had to opt into, but the checkbox did not mention spam or ads. Later versions did mention that ads would be displayed.
I’d like to repeat that I have chatted with the author of this plugin on a fairly long phone call and he shared his real identity with me. He prefers to remain anonymous, but is in control of the plugin once again and has been for a year at this point. WP Slimstat no longer contains any spam code, and has not for some time.
WP Maintenance Mode Plugin
Once we identified several plugins linked with Soiza, we started looking through the repository to find plugins using the same domains. We were surprised to learn that WP Maintenance Mode was involved. It is a very popular plugin with around 500,000 active installs. From June 20, 2013 to September 1, 2014, WP Maintenance Mode had code that allowed content to be remotely injected into a website without permission.
The versions that were affected are 1.8.9 up until the code was removed in version 2.0.0. At that point, ownership of the plugin changed hands to the new owners who appeared to remove the code.
I chatted to the new owners via email and they don’t have any information that can help us link this to other affected plugins. I also reached out to the previous owner and managed to connect with him via email but was not able to get any helpful data.
The one link we do have is the domain that WP Maintenance Mode was loading ads from. It was wordpress.cloudapp.net, one of the domains used by WP Slimstat which we confirmed was paid by jj@linkrocket.net. So this appears to, at the very least, be linked to the same advertiser that used Slimstat.
The difference with this plugin is that there was no opt-in required by the user. The advertiser could simply inject content into the website at will. You can find an example of the code in version 1.8.11 on this page.
This page on a hosting company website shows a user in 2013 asking why WP Maintenance Mode is slow in loading. It turns out it was contacting wordpress.cloudapp.net to load content in the background.
NewStatPress Plugin
We found this plugin was involved when searching for the domain associated with the plugins above. We found this post from 2013 where a user was reporting the plugin slowing down when loading something from wordpress.cloudapp.net.
NewStatPress would randomly select a WordPress hook like get_header, get_sidebar, wp_head or wp_footer and print out a decoded JSON blob which it fetched from the wordpress.cloudapp.net domain.
This plugin, WP Maintenance Mode and WP Slimstat all use the same domain, which is linked to jj@linkrocket.net.
This plugin ran this code from May 5, 2013 until June 29, 2013. The versions affected were 0.6.2 to version 0.6.7. You can see a sample of what the version 0.6.2 code looked like on this page.
I posted a contact request on this plugin’s support forum but did not get a response in time for publication.
Menu Image Plugin
In our research, we found that Menu Image was also loading ads and injecting them into site content. This post, where users are discussing spam being injected into the plugin, is what initially caught our attention.
The Menu Image plugin had opt-in ads that displayed if the user agreed to a long license that was vague in describing what would happen to your website. I chatted to the author via email and he was very helpful in helping us identify whether these ads are linked to the other plugins.
It appears that the author was paid by someone with a different name, tied to a different company. The domain used to load the content was apistats.net.
There is one tentative link: apistats.net at one point shared an IP address with the domain api.wp-stats.io which was a domain used by WP Slimstat which we linked to jj@linkrocket.net (that Soiza domain again). The api.wp-stats.io domain also shared an IP at one point with wordpress.cloudapp.net and wpcdn.io, which as we know are other domains used to serve content to these affected plugins.
Menu Image contained this code from July 7, 2016 until November 20, 2016 – slightly less than a year ago. The versions affected were version 2.6.4 to versions 2.7.0.
You can find a diff that shows when the code was added, in the file notice.php, on this page on github.
Weptile Image Plugin
This plugin caught our attention when we did a Google search for functions used by other plugins to inject content. This plugin also uses the notice.php file with the same function names as the Menu Image plugin. It also loads content from the apistats.net domain.
Weptile included code to remotely load content on July 2, 2016. It appears to have been removed from the repository on the same day.
According to this article, the plugin later changed ownership. The date the post was published is September 25, 2015, about 1 year before the injection code appeared.
The domain used to inject content was apistats.net which, as we pointed out above, does have a tentative link to Soiza and linkrocket.net.
I was not able to contact any authors associated with this plugin.
No Comments Plugin
This plugin caught our attention because it used the wpl.io domain to inject content into websites. That domain was hosted on the same IP address as wpcdn.io which we linked directly to Soiza.
The plugin contained code that injected content from April 25, 2014 until it was removed from the repository in October 2016. From version 1.1.5 the plugin contained code that could deliver spam.
The code in this plugin checked to see if a user was signed in. If the user was not signed in, the plugin would fetch a blob of content from the wpl.io domain, decode it and inject it. The plugin would print meta-data in the affected site’s header and replace keywords in the content with links. The links were hidden from view using CSS. There was no option to disable this feature.
I was not able to contact the authors of this plugin because it has been removed from the WordPress repository.
Financial Calculator Plugin
This plugin gets an honorable mention. It has never contained any spam code. However, the author, Ciprian Popescu, was kind enough to chat with me. It turns out that Soiza (pp@linkrocket.net) paid $600 to get access to this plugin but never used his access to add any code.
The date on the transaction was April 24, 2017. After we chatted, Ciprian reverified that Soiza no longer has access, and assured us that the plugin is safe.
A Coordinated Effort to Spam Via WordPress
What this research reveals is a coordinated effort by a malicious actor to use WordPress plugins to serve spam that started in 2013 and lasted until this month.
In some cases, the site owner had to opt in, but the opt-in message was either vague, misleading or obfuscated. In other cases, WordPress sites would serve ad content without the site owner being aware.
The content from these ad servers includes ads for payday loans and ads for escort services based in the UK.
How Plugin Authors Can Avoid Falling Victim
WordPress is now the most popular content management system in the world by a significant margin. It is important that we, as plugin authors, recognize that we are attractive targets for bad people. If they can infect just a handful of plugins with malicious code, it can be worth millions.
Stay secure and keep your code and customers secure. If you consider selling your plugin or a partnership, make sure you understand who you are selling to and what their history is. Also get a clear understanding of what their intentions are. Get references. You might also consider reaching out to the community, including Wordfence, to find out if anyone has any data on your buyer.
I would also strongly recommend to plugin authors to never give ‘commit’ access to a partner. Have them send you a patch or feature request and review and commit the code yourself.
Make sure your buyer or partner understands the plugin directory guidelines.
How WordPress Site Owners Can Avoid Spam in Plugins
As a WordPress site owner it is important that you keep track of which plugins are removed from the WordPress repository. In several cases, the plugins affected in this post were removed multiple times from the WordPress repository. If you are using Wordfence, it will notify you that a plugin you are using has been removed from the repository.
When you see a plugin removed, go to the support forum and ask the developer what happened. If they aren’t clear and transparent in their answer, you might considering moving on and using a different plugin.
Stay abreast of security developments by subscribing to our mailing list. When we discover that a plugin has been spamming, we immediately notify the community and take action.
If a plugin does include “terms” that you need to agree to, read the entire T&C document included, especially the end. In several cases the plugins affected did have an ‘opt-in’ checkbox with terms that said ads would be injected into your website. The problem was that the language describing the ‘ads’ was at the very end of a very long document.
If a plugin has an ‘opt-in’ checkbox for any kind of data sharing, make sure that it clearly describes what is being shared with or fetched from a remote server.
A Final Note
As a final note, I would like suggest that the WordPress.org maintainers enable two-factor authentication and enforce a strong password policy on the plugin repository. I’d like to suggest TOTP which integrates with password managers like 1Password.
These supply chain attacks will only get worse. This will probably be a large and complex project because it involves enabling two-factor on the code repository and other systems. So this will take time, because it risks breaking things.
Mark Maunder – Wordfence Founder/CEO.
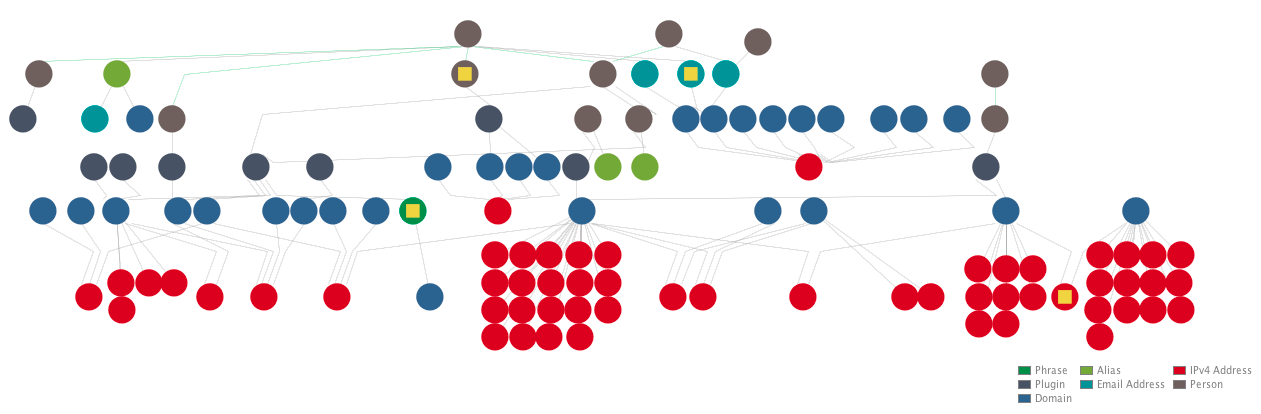
Credits: Thank you to all the plugin authors who we interviewed and who shared data with us that helped us compile the connections described in this post. They are listed at the top of this post. Thanks to Brad Haas who compiled the data we gathered into a Maltego investigative graph (pictured at the top of this post) which was invaluable when understanding the complex connections in this story. Special thanks to Åsa Rosenberg, Ryan Britton, Matt Barry, Colette Chamberland, Dan Moen and other Wordfence team members who provided valuable assistance. Thanks to Andie La-Rosa for editing.

Comments
9:51 am
You guys are doing amazing work. Seriously, keep it up! This stuff differentiates you from all the other run-of-the-mill WordPress security "experts" out there, and makes it continually clear you're the real deal.
10:01 am
Thanks Josh. Much appreciated.
9:57 am
This is first rate WP journalism. The depth of detail behind this piece is astonishing, Well done & keep up the good work.
10:00 am
Thanks David.
10:01 am
Ironic that one of the domains used to serve spam was called "stopspam.io" ...
10:02 am
Yeah it's quite funny.
10:08 am
Will there be no legal ramifications against this guy?
If there are no legal ramifications... fines & prison time... what s to deter others from doing the same on a wider scale , as you mentioned?
10:09 am
Hi Daniel,
We can't comment at this time. I'm replying to your post because I'm sure others have the same question. Folks, please don't ask because we have no data to share regarding this question.
Mark.
10:08 am
Thank you very much for your continued investigations and excellent reporting on this extremely important topic.
10:11 am
Thanks Ken.
10:09 am
You are amazing. Truly. Thank you for your hard work and brilliant sleuthing. I can't imagine what life would be like as a developer and website owner without Wordfence, and you just keep raising the bar.
10:11 am
Thanks Kimberly.
10:09 am
Dog with a bone or what...
Nicely done.
10:10 am
HAHA. Yeah. Actually I'm looking forward to putting this behind the team and I. Onward to other interesting projects!!
10:13 am
Thanks for watching out for us. I am not very techy when it comes to coding and such so I do use a few plugins. Thankfully none of these that are listed.
I'm so thankful I decided to upgrade to your Pro version. It's a small price for peace of mind. I suggest it to all the bloggers in my circles. We all work too hard to have our work compromised or destroyed. And keeping our readers' trust is worth every penny.
10:20 am
Thanks Toni. That means a lot to us. Much appreciated.
Mark.
10:15 am
Surprised to see on the list some of the popular plugins. How it shatters the trust in any plugin is painful to experience.
10:20 am
I don't think it should. These things happen and remember that much of this happened a few years ago - including the WP Maintenance Mode thing. The plugin has changed ownership since then. Many authors and the plugin team have learned from these experiences and the WP repo is stronger than ever today. Plus we've learned a lot and added those learnings to our capabilities. So we keep an eye on things too.
Mark.
10:16 am
Quite honestly the best reporting on anything WordPress related I've ever seen. Journalism at its finest. Please keep it up.
10:19 am
Thanks Chris!!
10:37 am
As usual you guys have written a well researched, fact filled and beneficial article. Keep up the great work.
10:47 am
I have had a recurring problem with spam popups and it turned out to be the SweetCaptcha plugin. Don't know if it is the same party causing these problems but warn people off nonetheless. Good job keeping us informed!
10:49 am
Thank you very much for all this info and research you provide us. You don't see see such high quality articles like this very often out there on the web.
Keep it up, and I love your plug-in. I install, and recommend your pro upgrade for every site I build.
11:20 am
Thanks for the very good write up. You guys do some very interesting and informative journalistic work on top of the excellent plugin you provide for free, of which I am an avid and loyal user.
11:22 am
Some plugins line NGG ask to connect to fremius.com (or something like that) for basic non-identifyable information.
Not saying anything bad about NGG or fremius.com but, how can I be sure they are good (or anyone else asking for basic usage data is good)?
11:37 am
Plugins connecting to external servers is totally fine. Wordfence connects to noc1.wordfence.com to do a lot of the work involved in scanning your site. We grab the firewall rules and malware signatures from that server. If this capability is removed it would reduce the awesomeness of a LOT of plugins.
There are just a handful of bad apples that use this capability for bad things.
12:14 pm
First off, let me just say that I am a HUGE fan of your plugin and cannot even count the number of times it has protected my site from attack.
Second, I've been following this article series and I am extremely grateful for the in-depth info you have shared.
I think what this spammer did is despicable, and as an Internet Marketer since 2008, it pains me to see bad actors like this who are responsible for giving the entire industry a bad name.
In closing, your journalism and plugin are the best out there, and I will continue to look forward to your reporting.
Thanks for being the class act that you are!
12:17 pm
Thanks Chris.
12:17 pm
I have (had) No Comments on one of my sites, the header contains the following contact details for the author:
[Removed by moderator]
12:23 pm
Thanks Paul. I think the post above has probably made them aware. They're welcome to post here.
12:28 pm
Mark,
If there was a Pulitzer Prize for cyber security journalism, I suspect you and your team would win hands down. This is really outstanding investigative sleuthing/writing and speaks volumes about why we use WordFence on all the websites we build and manage.
Now, if you can just turn your attention to the Equifax problem, I would feel much better about my compromised PII.
Appreciate the hard work, Mark.
12:30 pm
I'm afraid that ship (or data in this case) has sailed Jim. Sorry about that.
Just get comfortable with your private information including social security number being out there for everyone to see, and you'll be just fine. It's a brave new world.
Mark.
12:41 pm
Yes, after spending the last 25 years in tech, I've gotten used to the idea that if you are online, then nothing is truly private. It's the extent of these aggregated databases full of private information (far more than just SS #s) that should trouble all of us. It's hair-on-fire time for companies both small and large. Cybercrime is a "thing" and needs dedicated professionals to help mitigate the problem. Many of my less informed friends just shrug their shoulders over the Equifax debacle. Many people just don't realize how serious this really is. And, don't start me on the problem with our power grids and other infrastructure weaknesses :-) Again, thanks for all your efforts. It's very much appreciated.
1:22 pm
Huge kudos for seeing this through and for digging so deep!
Using your product on a dozen sites, and will continue to expand its use and recommend it to others.
Thanks so very much,
Tearo
1:39 pm
I second all the positive words already posted. Wow.
Reading these reports I wondered: can Mason Soiza have done it all by himself? I doubt it. It takes coding skills, financial skills etc. etc. What can the WordFence team say about the coding: is it easy stuff? And what about organizing these websites etc.?
1:48 pm
:::stands and applauds::: Truly outstanding detective skills and journalistic work. I agree with a previous poster - you deserve a pulitzer prize for this project. Thanks for watching our backs and giving me, as a business owner, comfort in the dynamic security environment of wordpress.
3:06 pm
Great work and thank you. You just made me realize I need to upgrade to your pro version. Keep up the good work.
3:26 pm
Nice series of articles, truely fascinating to read and I hope the person or persons behind this have stopped and instead try to make an honest living. Idle hope maybe, but hope nonetheless :)
"I’d like to suggest TOTP which integrates with password managers like 1Password."
While I'm a very strong proponent of 2FA, I believe you meant 'TOTP, for which a separate password-protected app is required'.
After all, why would you want to combine the storage and auto-filling of your strong passwords with two-factor authentication features in a single app/program? If anyone were to gain access to that one app, your 2FA-secured sites would be wide open. But... maybe I'm misunderstanding how 1password integrates TOTP...
3:32 pm
2 factor means you use at least two out of the 5 factors to authenticate yourself.
In this case you're verifying that you know something and that you have something.
You know your password.
You have your 1password vault which is on your physical workstation. So you have your physical workstation.
The interesting point you make is that if an attacker just compromises one of those factors, they can authenticate with both factors. The 1 factor to go after in this case is 1password.
3:52 pm
Hi Mark,
You mention in your article that one should check the support forum of the plugin for reasons that it might have been removed from the repository. Normally you would google the plugin name, find the usual plugin homepage (Description) and click on Support right there. As the homepage is not available anymore for removed plugins, it would be quite handy to include a link to the support page in your notification mail. That saves us some time figuring out wat the right url is.
Jos
6:10 pm
Good idea. I guess the support page does still exist after they remove the plugin from the repo.
Yup it does, just confirmed that display widgets still exists: https://wordpress.org/support/plugin/display-widgets
Will get this added. Thanks.
Mark.
7:06 pm
The main page etc... still exists, but only the plugin team (and maybe moderators, not sure on this point) and current contributors can view the main plugin page, other users are redirected to the plugin search page.
I've removed four of my plugins from the repository (requested the plugin team to close them), so familiar with what's accessible etc... when a plugin has been closed.
What's publicly accessible:
Support Forum - wordpress.org/support/plugin/PLUGIN-SLUG/
Review System (extension of the forum) - wordpress.org/support/plugin/PLUGIN-SLUG/reviews/
Dev Log - plugins.trac.wordpress.org/log/PLUGIN-SLUG/
SVN - plugins.svn.wordpress.org/PLUGIN-SLUG/
Code - plugins.trac.wordpress.org/browser/PLUGIN-SLUG/
RSS Feed - plugins.trac.wordpress.org/log/PLUGIN-SLUG/?limit=100&mode=stop_on_copy&format=rss
It's funny to see the plugin still has 4.7 out of 5 stars :-)
So it's only the main page and the advanced page (with download stats) the public can't access.
Strange way of doing things if you ask me, would make more sense to keep the main page and add some info why/when the plugin was removed and if a site is at risk if XYZ isn't performed and if the plugin team don't want new installs (as is the case for the Display Widgets plugin) remove the download link.
I guess it's easier just to leave users in the dark and at risk!
David Law
4:07 pm
Thanks for these posts, i've been following them with shock.
Quick question: if the original developers sold the plugins, how they regained access? I was thinking that if you sold the plugin you lose the admin login and everything related. The new owner paid for it so can do anything they want. What am I missing?
6:09 pm
The relationship varied. In the case if Display Widgets the spammer bought the plugin outright and added a backdoor. So the plugin team just took it over, locked the guy out and reverted it to a healthy version.
In some cases the spammer paid for access to the repo. The dev was able to lock the guy out and take it back.
In some cases the dev was given code to add (I think. I haven't confirmed this.) and they could just back out that change.
4:09 pm
Excellent work in exposing this spammer. Eye-opening reporting. I have a small plugin but I'm not a programmer so I hired out the work on Elance (now Upwork) of actually coding my idea into fruition and this really has me worried. I vetted the programmer. He did great work. The plugin works great. But, boy, what a nightmare if he added some bad stuff to it and I would be clueless. I'm the only one with commit access though. You've given me something to be even more vigilant about in the future when relying on freelance coders.
4:14 pm
Mark, you might also want to look into the history of plugin called "Sweet Captcha" -- here's a blog post from 2015 from Security Net that explains the problem -- https://blog.sucuri.net/2015/06/sweetcaptcha-service-used-to-distribute-adware.html
And Wordpress support forum posts: https://wordpress.org/support/plugin/sweetcaptcha-revolutionary-free-captcha-service/
It doesn't look like it was part of the same operation - different types of ads -- but same underlying problem.
6:19 pm
Wow! Very detailed article as always! Are these sites and IP addresses already blocked when WordFence is active? I really want to know how WordFence is handling this kind of issues specially on affected sites. Thanks!
Another replacement/alternative for Display Widgets is [removed by moderator because these are on a .com commercial site, not in the repo]
6:28 pm
We blacklisted associated URLs and alert if they're found in your source or anywhere else. We're also working to create awareness of which plugins are affected and their current status.
6:54 pm
Sounds reassuring. Does the scan detects the occurrence on the database table? This will be of great help to make sure that infected sites can be cleaned properly. Thanks!
2:02 am
What do you think about this strange update?
https://es.wordpress.org/plugins/quick-adsense/
Active Installs: + 100,000
Member Since: August 24th, 2017 (https://profiles.wordpress.org/quickadsense#content-plugins)
Regards
1:38 pm
Yes! That looks very, very suspicious. I would uninstall it immediately. Lsat update was 4 years ago, quickadsense.com was registered on 2017-08-23, the user name "quickadsense" is following the trend, the update is causing a lot of complaints. I looked through the code and see that some new large files were added.
2:13 am
Look at that code, it's a mess. Also, it looks like it's been copied from various other plugins, as the syntax is different.
https://plugins.trac.wordpress.org/browser/quick-adsense/trunk/quick-adsense.php?rev=709873
2:22 am
Great work.....this could be made into a drama series for TV? Idris Elba could play the part of Mark Maunder & Mason Soiza by Ray Winstone. Wheres my pen! Thanks for your efforts.
9:56 am
What more can I say that has not already been said. Thank you for all your hard work. I am so glad I found WordFence back in 2015, and will continue to use it as long as I have a WordPress site. The research, the security, the blogs are all so very helpful. THANK YOU!!!
10:53 am
Just a question about this part of the post: "If you are using Wordfence, it will notify you that a plugin you are using has been removed from the repository."
Is that notification controlled by the Wordfence option "Scan plugin files against repository versions for changes"?
Or, does Wordfence notify users of removed plugins from the repository regardless of which checkboxes are selected on the Wordfence Options page?
11:23 am
We notify you regardless. And it will be a 'Critical' level notification.
9:47 pm
Very thorough explanation & avoiding getting hacked with spam code is so important especially with a large domain. I am going to have to give up Comment Luv Premium because I think the programmer is just not able to keep the plugin up to date. I would guess any plugin that has not been updated in 2 years should be replaced with something more current if you can find one.
8:05 am
If you look at Semrush, Payday Loans Now were penalised when this all went public - https://www.semrush.com/uk/info/paydayloansnow.co.uk?db=uk
If you check their rankings today they are back! Search in Google.co.uk for "payday loans UK" and you will see they are in their old spot.
The original penalty was well deserved, I can't understand how they have came back today in their old positions.
11:36 am
Hi, we are the original authors of Weptile Image Slider Widget Plugin and we would also like to provide all details we have with you guys. Hoping we can help you on your great cause and get these spammers be found and publicly announced.
You can contact me directly via pm at weptile dot com.
Quick notes:
1. We were first contacted by Will Verroch (willverroch@gmail.com) July 17th, 2015.
2. We transferred the ownership on September 25th, 2015.
3. Very soon after we transferred the plugin ownership, we realized the spam code they injected. We reported but got no solid response from WP repo.
4. We did report them for a few things, and finally in 2016 we reported them to be using our brand name in their plugin (they were supposed to remove our name and replace it with their's - doh, they were lying all along). So that's when the plugin was finally removed from the WP repository.
5. They sent us money over Escrow.com
6. We had emailed over 20 times until it was over. They seemed all professional, answered clearly and directly. We had no idea what their actual goal was. Plus they paid good for a plugin we basically made no money from. (looking at the $15k they payed for the widget plugin, our $1.5k looks funny though :) )
7. Anything else you'd like to ask us, or if you'd like to read all our emails with them, please contact us.
P.S. I'd love it if you could fix our name and the plugin's name on the blog posts. The plugins name contains our brand "Weptile" but that's not the name of the plugin :) Please call the plugin with it's full name if you can :)
11:47 am
I wanted to add a few more info I found scanned the old emails:
8. The contract we signed was sent to us from sales@afkay.com through hellosign.com. The contract page now gives a 404, so I guess we can't read what was in there any longer. But the initial signiture request email says:
"Peter Navrides (sales@afkay.com) has requested your signature"
I guess they're either a bunch of people, or some guy is using lots of fake names and emails.
9. The INVOICE ADDRESS we've been told to send the invoice was the following:
AFKAY LLC
9 E Loockerman St STE 3A-641
Dover, DE 19901
United States
10. Just checking the invoice now, I see we've received $2500 for the plugin ownership transfer back then. Their initial offer was $150 per 10k downloads. We had a little more than 10k downloads back then, so we said we will not sell the plugin. Then they offered more. Asking for a price. We bargained, and ended up with $2.5k deal. Back then I remember feeling like we won a small lottery. An offer like this for a plugin that we built to help out - for free.
Too good to be true I guess. I apologize on behalf of our team from everyone that was using the plugin back then. I guess we should republish a better free plugin as an apology...
12:00 pm
P.P.S. You can contact me at skype: ufuk.erdogmus (weptile) as well.
12:38 pm
WordPress website owners should get together and start a class action against Mason Soiza to disgorge him of his ill-gotten profits and make him pay punitive damages for his ad spam.
5:46 pm
Found this new one : https://wordpress.org/support/topic/fs-contact-form-no-longer-in-wp-market/ that you might want to investigate and add on the list too. Thanks!
12:31 am
I can't be the only one that thinks there is something very screwed up about the way plugins are being dealt with.
The team at Wordfence are heroes and everyone owes them a big thank you. It is not just people who had these plugins installed: It is everyone who will look more carefully at every plugin they are thinking about installing.
But why is it the team at WordFence who are finding this? It is not the kind of novel code that Google or Facebook pay big bounties for, is it? Why are these things in the repository at all?
Is there a team of people working for WP/Automattic who are dedicated to examining and vetting everything that is submitted to the repository?
If not, then why not? There is too much riding on this for the safety to be dealt with on careless basis, is there not?
6:47 pm
Here is another plugin - the "original author of SI CAPTCHA" has linked to this Wordfence post.
Otto says, "I have released a clean version of this plugin, with the malicious code removed. Version 3.0.3 is clean"
https://wordpress.org/support/topic/where-did-the-plugin-go-2/
11:03 am
I thought I read recently that WordFence now lists plugins that have been removed from the WordPress plugin repository. Is this not the case? Did I misunderstand this point?
I ask because Fast Secure Contact Form has been removed, apparently within the past 24 hours. WordFence dashboard says nothing at all about it being removed, only that it has an available update.
Can you guys confirm this is the original plugin authors page and that the current update for this plugin is in fact clean and safe to use, please?
Here is the page I found:
http://www.fastsecurecontactform.com/
It says the page is by Mike Challis, that he had recently sold the plugin and the plugin was infected by the new owners.
It further states that WordPress moderators have released a hidden clean version of this plugin, with the malicious code removed. Version 4.0.56 is clean, and has the various changes from the new owner backed out.
Thank you so much for all you do to help all of us protect our sites. You guys ROCK!
2:47 pm
You should have received that alert. If not please contact support.
4:46 am
This has happened to another very fine contact form plugin I have used for years. The author sold it in June, and the buyer injected code to spamvertize pay day loans from his own server. I don't see this on your list of affected plug ins. It was si-contact-form. Purchased by "fastsecure". Wordfence alerted me that it had been removed from Wordpress repository, and gave this link: http://www.fastsecurecontactform.com/. Mike Challis is the original developer, who I have paid over the years everytime I used his form on a site. I think perhaps Wordpress needs to develop a rating system for the developer/seller in addition to the plug-in itself. Similar to Amazon or EBay. I can purchase a product with a good rating, but I might not want to buy it from a seller with a bad rating. The bad guys are taking advantage of the original developer's good reputation. So now what do we do with sites using this form, which appears to be ok for the moment?
7:03 am
The author of the SI Captcha Anti-Spam plugin reports that his work was also hijacked for this scam. See https://wordpress.org/support/topic/where-did-the-plugin-go-2/.
How many more are lurking out there, I wonder?
1:43 pm
From here my sincere congratulations for all the research and information on the subject "Souza".
During the last week I informed all my readers (on my blog), listeners (in my podcast) and viewers (in periscope/youtube) thanking you in all cases to you and to Wordfence the work done.
I do not understand why WordPress.org does not promptly inform all users of this type of cases. I do not understand why we are not warned when a plugin is removed from the repository and what is worse yet ... I do not understand how a delinquent of this kind can update a plugin with malware 4 times and go unpunished.
I reiterate my thanks. Greetings from Spain.