Cryptocurrency Miners Exploiting WordPress Sites
 During the last month, the information security media has paid a lot of attention to cryptocurrency mining malware. The Wordfence team has been monitoring the situation, and we are now starting to see attacks attempting to upload mining malware, and site cleaning customers that are already infected.
During the last month, the information security media has paid a lot of attention to cryptocurrency mining malware. The Wordfence team has been monitoring the situation, and we are now starting to see attacks attempting to upload mining malware, and site cleaning customers that are already infected.
In this post, you’ll learn what cryptocurrency mining is, what’s in it for the attackers, how to check if you have this issue and what to do about it if you do.
Cryptocurrency Mining Attacks on WordPress
For those of you who aren’t up to speed, cryptocurrencies are digital currencies that can act as an alternative to traditional currencies. Examples include Bitcoin, Litecoin, Ethereum and Monero, among many others. Cryptocurrency mining is a computationally intense process that contributes to the operations of the cryptocurrency network while generating new currency. It takes a massive amount of computer resources to generate meaningful income. People interested in cryptocurrency mining generally need to invest in expensive equipment and solve for the power consumption and heat generated by hardware.
Recently online platforms have emerged that allow website owners to harness the computing power of their website visitors to mine cryptocurrency. Website owners simply sign up for an account and add some JavaScript to their site. The downside is that their visitors’ experience is likely quite poor as their computer resources are then put to work mining. It is debatable whether website visitors will ever view this practice favorably, but it will be interesting to watch the trend evolve.
We saw the first attack on a WordPress site attempting to embed cryptocurrency mining code on September 17. Attack volume has been very low and unsophisticated so far. However, our Security Services Team is starting to see hacked websites with this malware, so the attackers are starting to have some success.
The attacks we have analyzed are all trying to exploit well-known security vulnerabilities that have been around for a long time; for example, the Gravity Forms exploit from mid-2016, or the Joomla com_jce exploit from early 2014. We have also seen quite a few attempts to insert mining code using compromised WordPress administrator accounts, as well as some attacks using compromised FTP accounts.
How Attackers Profit From Cryptocurrency Mining Malware
Attackers are embedding Javascript code from Coinhive (update: now defunct) on websites they have compromised. Coinhive provides a way to mine a cryptocurrency known as Monero. Monero differs from other cryptocurrencies like Bitcoin, in that it does not give miners who use GPUs or other specialized hardware a significant computational advantage. That means it is well-suited to use in web browsers, executing as JavaScript on consumer CPUs.
Site owners who place the Coinhive code on their websites earn Monero currency. The Coinhive code uses site visitors’ computational resources to mine Monero. An attacker can place the Coinhive code on thousands of websites and earn Monero from the mining that happens in site visitors’ browsers.
The following is an example of embedded Coinhive code that will mine Monero currency:
The research team at Checkpoint analyzed the profit potential for an attacker planting this malware. They concluded that an attacker successful enough to average 1,000 concurrent users across all infected sites would generate $2,398 in monthly revenue.
We think these attacks will grow in popularity very quickly given how lucrative they are. Attacks that attempt to embed cryptomining malware are currently unsophisticated, but we expect to see an increase in the sophistication of attacks as word gets out that this is a lucrative enterprise. We also expect these attacks to target higher-traffic websites, since the potential to profit increases greatly with higher numbers of concurrent site visitors.
How to Check if Your Site Is Infected With Cryptocurrency Mining Malware
The Wordfence firewall blocks attacks attempting to infect sites with this malware. We have added detection capability to Wordfence for cryptominer scripts. This means that the scanner will warn you if it detects this type of script on your site. It also means that the Wordfence firewall will block any uploads that contain the script.
Wordfence Premium customers currently already have access to this detection capability. Free users will get access to this capability on November 24 via the Community version of the Threat Defense Feed.
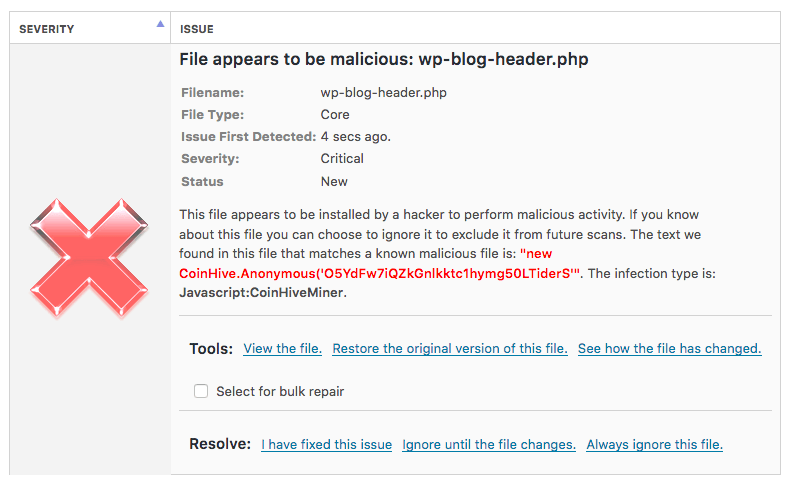
It is important to make sure you detect an infection quickly if an attacker should manage to slip through your defenses. Below is an example of a scan finding that would indicate this infection exists on your site.
(If you have intentionally added a cryptominer script to your site, of course, you can simply ignore the finding.)
Some cryptomining malware may be more hidden or obfuscated, so always pay attention if many of your visitors start reporting poor performance by their browser or computer while visiting your site.
A few hackers have adjusted the miner settings so that it only uses only a portion of the available CPU power, or so that only one instance of the miner script can run at a time (even if it’s open in multiple tabs).
![]()
But many of them are still set to use 100% of available resources, no matter what.
![]()
Changes in Attacker Business Models
New business models are constantly emerging for attackers. Historically, attackers would use compromised websites to generate spam content or spam email. In the past decade, ransomware has gained popularity among attackers, as it allows them to extort money from victims. More recently, using stolen computational resources to mine cryptocurrency has emerged as a way for bad actors to profit from compromised systems.
This emerging business model has now made its way into the WordPress ecosystem as a way for attackers to profit from compromised WordPress websites and the computational resources of website visitors. It is imperative that WordPress site owners deploy a firewall and malware scan on their sites to quickly detect this new threat and ensure that their site visitors’ resources are not hijacked to mine cryptocurrency.
What to Do If Your Site Is Infected With Cryptocurrency Mining Malware
The most reliable way to recover if your website is hacked is to use our site cleaning service. Our team of experts will clean your site and get it back online as quickly as possible, and the service includes a detailed report and a 1 year guarantee. You can also use the Wordfence site security audit to do a comprehensive security inspection of your website.
If you prefer to try to fix any infection yourself, you can follow our guide to fixing a hacked website with Wordfence.

Comments
11:04 am
It should be noted that Coinhive (and it's adblocker-friendly authedmine.com) are NOT the problem here. Legitimate sites, faced with declining revenue, have placed Crypominers on their sites to offset this loss of ad revenue. Yes, some hackers are hijacking this, and THAT is bad, but the presence of the code is not an indication of an infection.
Example #1: I have a page dedicated to people who want to support my efforts. On that page you can make a PayPal donation, click through to Amazon using my affiliate code, and there's a Coinhive cryptominer there, too. Go take a look: http://www.JoeLevi.com/thanks.html
Example #2: There is a concept called "proof of work" which essentially runs a pre-determined number of computations. Once that threshold has been met and submitted, a value is returned. This can be set up to operate as a Captcha. If someone wants to log in to your site, just like Google's "I am not a robot" captcha, this method could be used to incur a compute expense on the computer of the person logging in. This not only slows down brute-force login attempts on your site, but for a bot that's brute-forcing to have to spend thousands of compute cycles per login, this kind of captcha can help reduce the impact on OTHER (non-captcha'd) login pages, too.
In conclusion, there are some very legitimate use-case scenarios which can be employed through this type of technology. Sure, some people are exploiting it, and some people are hijacking. The article doesn't offer this perspective, so I wanted to provide this information for the reader's consideration.
- Joe Levi, Redoubt Solutions, LLC
Security and Information Services
11:43 am
Thanks for your input Joe.
3:41 pm
Joe Levi, these things could have been implemented correctly in the first place. Instead, coin-hive made a rather silly mistake, and now people are treating it as malware because that is in fact the main use of this code. The "legit" cases of coin-hive is less than 1% of the total. People are exploiting it and the bottom line is simple: Browser based coin mining is now officially a menace, and it will never be considered in any way legitimate ever again. It will be blocked, it will be incorrectly called a "virus", and it will be banned in all possible ways.
It's dead tech before it even started because of this poor, poor implementation.
10:59 am
Otto, I hear what you're saying, but I'd like to see if I can put it in the context of something we already know to see if it might change your opinion.
Today we have ads on our sites which are delivered by any number of providers. These ads began as images, adding additional load-time and bandwidth to the pages the users' load. They didn't ask for this. They weren't given the ability to "opt-in". Their bandwidth was "stolen", their compute cycles were "stolen", and their screen real-estate was forcefully "occupied" by an ad they didn't ask for.
What's worse, since these images were served by other systems (not the site which the user was visiting), all their IP and header data were available to this 3rd Party - again, without option.
But it wasn't just images which were being served. It was Flash/Shockwave objects, which were mini-programs which could monitor activity on the page. Again, without option.
Now, it's not Flash as much as it is IFRAMES - entire web pages with images, scripts, css, cookies, and more. All this delivered without asking if they can use your bandwidth, your compute cycles, your screen real-estate, or your disc's storage space.
That's the state of ads today - but no one seems to care.
Did advertisers make the same "silly mistake" which you argue Coinhive did by not forcing a pre-load opt-in? Should people treat ad networks as "malware", because they, like Coinhive, use your system resources without your explicit authorization? Are people not "exploiting" ad networks now in the same fashion which you argue they're "exploiting" Monero mining?
Aren't ad networks now a "officially a menace, and it will never be considered in any way legitimate ever again", based on the same arguments you made about Coinhive?
Shouldn't people also want to block ad networks, call ad networks a "virus", and ban them "in all possible ways".
Why aren't ad networks "dead tech before it even started because of this poor, poor implementation"?
I ask these questions not to argue, but to open the conversation about the resources which are currently being sequestered by ad networks (which nobody seems to care about), and to try and determine why that is somehow an acceptable non-optional use of resources, but crypto-mining is somehow not.
- Joe Levi, Redoubt Solutions, LLC
Security and Information Services
11:03 am
If I'm visiting a website that has cryptocurrency miners running them, unbeknownst to site visitors, I want to know about it. Sure, you can argue this is another form of advertising as it generates revenue for sites suffering from ad blocker usage, but IMHO it's an underhanded method.
Moreover, Wordpress sites tend to have a lot of embedded code in the pages due to WP add-ons that require it to run. As a website admin and user, I don't thinks it's a good idea to be impacting page load times more with additional page code that the browser needs to load/interpret.
In sum: this is not a best practice.
11:07 am
Obviously any hack/exploit is bad, and someone hacking thousands of sites to gain benefit of mining is likely going to go unnoticed longer than a hacked site that redirects or popups spam /malware, so this is a more subtle way of stealing off of other site traffic.
I do think that in general cryptomining on sites as a means of revenue may be a good alternative if done legit with disclaimers as a way to go banner ad free, remove advertisements to create alternative revenue source but only for sites you own/manage of course.
11:10 am
Monero as a cryptocurrency has a lot of potential and some really good tech, and in-browser mining has some legitimate uses. Sad to see it abused this way, it gives both browser mining and Monero bad reputations that they don't deserve. Thanks for adding checks for these to the scanner, hopefully with enough alertness and pressure the bad actors will find it too much trouble and move on to something else.
11:22 am
This is good information about a possible new hack on our sites. But, since this is really "infecting" visitors to sites, I would like to learn more about being able to detect that as a visitor - not just by noticing higher CPU usage. I often have many tabs open and do sometimes notice my CPU pegged and quit, but which site should I now avoid? Tools to empower visitors would create a natural boycott to make this unsuccessful.
12:34 pm
Hi guys. I had uncovered info about this coin mining in browsers becoming a problem in my security research and was literally just about to write to you all about it today. I'm glad you're aware of and on top of the problem. As a user, I'm very leery of this and have already installed a Firefox plugin to prevent coin mining in my browser. Even if website owners intentionally add mining code to their site with the best of intentions, it's very possible, even likely, that they would get low quality or abusive or even malicious code running on their sites which would harm the users. As a user, I MIGHT allow mining on my browser if a) I REALLY like the site. b) They give me great free content while encouraging me to provide revenue. c) They get my EXPLICIT permission to mine. d) They GUARANTEE where the money goes and honor that. e) They let me set the max cpu usage per tab and per site in 1 % increments and honor that. f) They let me determine whether background operation is allowed assuming it's even possible. g) They allow me to change or revoke my permissions at any time and honor that. and h) The use only reputable / credible mining providers. If I clear out my history and cookies (assuming cookies are used) and go back to the site, it should NOT mine, and should get my EXPLICIT permission all over again. Note that for many desktop computers in the continental USA, pegging the cpu will use about 100 W of extra power and, if done 24 / 7, will cost about $ 7 / month extra on your electric bill. This obviously depends on the computer, and the electric billing rate. Note also that pegging the cpu will cause your computer performance and responsiveness to go down the drain.
Thanks for all the great work you all do.
Ron
4:08 am
I agree with Joe. He summed it up right there.
7:44 pm
I'm also intrigued to see where this goes as regards to bad actors abusing a legitimate service.
I find that the Chrome extension minerBlock is working well at detecting pages that are running these mining scripts. Haven't detected a whole lot just now, but they are certainly out there.
Good to hear that Wordfence is now scanning for these.