PSA: Attackers Actively Exploiting Critical Vulnerability in Essential Addons for Elementor
On May 11 2023, Essential Addons for Elementor, a WordPress plugin with over one million active installations, released a patch for a critical vulnerability that made it possible for any unauthenticated user to reset arbitrary user passwords, including user accounts with administrative-level access. This vulnerability was discovered and responsibly disclosed by security researcher Rafie Muhammed.
Over the past few days we’ve seen millions of probing attempts for the plugin’s readme.txt file, which are likely to be attackers probing for the presence of the plugin to build a target site exploit list, along with over 6,900 blocked exploit attempts. Our attack data is limited due to the fact that the rule only triggers if the plugin is installed on a site with a vulnerable version, but a programmatic exploit was made public on Github on May 14th. This is the type of vulnerability that tends to see widespread attacks due to a combination of a large install base, ease of exploitation, and severity of impact, and we anticipate that exploit attempts will only ramp up from here.
Wordfence Premium, Care, and Response customers received a firewall rule the same day the issue was disclosed on May 11, 2023. Wordfence free users will receive that same protection 30 days later on June 20, 2023. Considering how easily this vulnerability can be successfully exploited, we highly recommend all users of the plugin update ASAP to ensure their site is not compromised by this vulnerability.
Vulnerability Details
Affected Plugin: Essential Addons for Elementor
Plugin Slug: essential-addons-for-elementor-lite
Affected Versions: <= 5.7.1
CVE ID: CVE-2023-32243
CVSS Score: 9.8 (Critical)
CVSS Vector: CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
Researcher/s: Rafie Muhammed
Fully Patched Version: 5.7.2
The vulnerability patched in Essential Addons for Elementor allowed for attackers to reset passwords for arbitrary accounts on any of the one million WordPress sites running the plugin. This was due to the fact that the reset_password function did not adequately validate a password reset request with a password reset key, so attackers could simply supply a valid username, obtain a valid nonce from the site’s homepage, input random data for the remaining fields, and reset the supplied users password to whatever they chose in one simple request.
WordPress doesn’t consider usernames to be sensitive information which means attackers can easily enumerate a site looking for valid usernames. Additionally, site owners often forget to change the default username making it possible for attackers to use common default usernames such as ‘admin.’ This makes it much easier for attackers to uncover valid accounts that they can compromise in order to elevate their privileges on the site. Once the attacker is logged in as an administrator, they have free rein to perform actions like installing plugins and backdoors to further infect the site, server, and any unsuspecting visitors.
A Look at the Attack Data
Plugin Discovery Probing
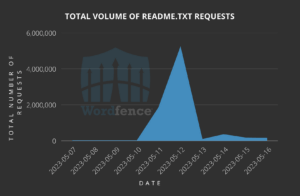
The first interesting trend we noticed is that immediately following the disclosure of the vulnerability on May 11, 2023 readme.txt probing attempts for Essential Addons for Elementor immediately spiked and remained relatively higher than normal over the course of a few days. While there are services that probe installation data for legitimate purposes, we believe this data indicates that attackers began looking for vulnerable sites as soon as the vulnerability was disclosed. Over 5,000,000 readme.txt probs were made just the day after disclosure.
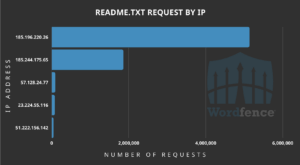
Top Offending IP Addresses Engaging in Discovery
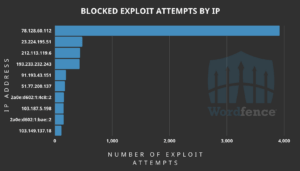
Top Offending IP Addresses And Total Number of Exploits Blocked
In the past 5 days, we have blocked over 6,900 attacks with the top attacking IP being 78.128.60.112. We have also detected and blocked a few hundred exploit attempts utilizing the exploit that was released two days ago. Again, our data is limited due to the nature of the WAF rule, however, it’s worth noting that all of the 6,900 requests we blocked would have likely led to site compromises if they did not have Wordfence Premium installed.
Indicators of Compromise
One obvious sign of infection is if a site’s administrator is unable to log in with the correct password as it may have been changed as a result of this vulnerability, and the site is running Essential Addons for Elementor version 5.7.1 or older. We also recommend checking for newly added malicious administrators, as these may have been added to maintain persistence.
We have begun tracking infections on sites running a vulnerable version of the plugin, and though no clear pattern has yet emerged, sites running outdated versions of the plugin were already at significantly higher risk of infection than our average user.
User Agents
- The public exploit uses the following User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/58.0.3029.110 Safari/537.36 Edge/16.16299
Look for requests in a site’s access log with the following originating IP Addresses:
- 78.128.60.112
- 23.224.195.51
- 212.113.119.6
- 193.233.232.243
- 91.193.43.151
- 51.77.200.137
- 2a0e:d602:1:4c8::2
- 103.187.5.198
- 2a0e:d602:1:bae::2
- 103.149.137.18
Conclusion
In today’s article, we covered a Critical-severity vulnerability in Essential Addons for Elementor that allows attackers to easily take over websites by resetting the password of any user, including administrators. We have begun tracking attack data for this vulnerability and expect attacks to ramp up as the vulnerability is trivial to exploit, has a wide install base, and is highly impactful, making it incredibly attractive to attackers.
Wordfence Premium, Care, and Response customers received protection against this vulnerability via a firewall rule on May 11, 2023, and Wordfence free users will receive the same protection 30 days later on June 20, 2023.
Even if you have already received a firewall rule for this issue we urge you to ensure that your site is updated to at least version 5.7.2 in order to maintain normal functionality, as this vulnerability is severe. If you have friends or colleagues running Essential Addons for Elementor, be sure to forward this advisory to them, as hundreds of thousands of sites still remain unprotected and unpatched.
If you believe your site has been compromised as a result of this vulnerability or any other vulnerability, we offer Incident Response services via Wordfence Care. If you need your site cleaned immediately, Wordfence Response offers the same service with 24/7/365 availability and a 1-hour response time. Both these products include hands-on support in case you need further assistance.
If you are a security researcher, you can responsibly disclose your finds to us and obtain a CVE ID and get your name on the Wordfence Intelligence leaderboard.
I’d like to say a special thank you to my colleague Ramuel Gall, Senior Security Researcher at Wordfence, for his assistance on this research and post.

Comments
11:41 am
One of my sites was hit by this on Saturday, May 13 at a little after 1 AM EDT. The admin username is unique on my site so the exploiters must have some way of figuring out the usernames.
I did have accesses from 78.128.60.112. Here are the log entries:
78.128.60.112 - - [12/May/2023:22:16:57 -0700] "GET /index.php HTTP/1.1" 301 - "-" "Mozilla/5.0 (Windows NT 6.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/65.0.3152.119 Safari/537.36" 316 **0/316978**
78.128.60.112 - - [12/May/2023:22:16:58 -0700] "GET / HTTP/1.1" 200 24235 "-" "Mozilla/5.0 (Windows NT 6.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/65.0.3152.119 Safari/537.36" 1582 **1/1582285**
78.128.60.112 - - [12/May/2023:22:16:59 -0700] "GET /wp-json/wp/v2/users HTTP/1.1" 404 114 "-" "Mozilla/5.0 (Windows NT 6.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/65.0.3152.119 Safari/537.36" 1059 **1/1059539**
78.128.60.112 - - [12/May/2023:22:17:00 -0700] "POST /wp-admin/admin-ajax.php HTTP/1.1" 500 184 "-" "Mozilla/5.0 (Windows NT 6.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/65.0.3152.119 Safari/537.36" 5431 **5/5431547**
78.128.60.112 - - [12/May/2023:22:17:07 -0700] "POST /wp-admin/admin-ajax.php HTTP/1.1" 200 111 "-" "Mozilla/5.0 (Windows NT 6.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/65.0.3152.119 Safari/537.36" 1142 **1/1142531**
78.128.60.112 - - [15/May/2023:21:33:53 -0700] "GET /index.php HTTP/1.1" 301 - "-" "Mozilla/5.0 (Windows NT 6.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/65.0.3152.119 Safari/537.36" 341 **0/341764**
78.128.60.112 - - [15/May/2023:21:33:54 -0700] "GET / HTTP/1.1" 200 30328 "-" "Mozilla/5.0 (Windows NT 6.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/65.0.3152.119 Safari/537.36" 1162 **1/1162941**
78.128.60.112 - - [15/May/2023:21:33:56 -0700] "GET /?author=1 HTTP/1.1" 500 2614 "-" "Mozilla/5.0 (Windows NT 6.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/65.0.3152.119 Safari/537.36" 211 **0/211270**
78.128.60.112 - - [15/May/2023:21:33:57 -0700] "POST /wp-admin/admin-ajax.php HTTP/1.1" 200 63 "-" "Mozilla/5.0 (Windows NT 6.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/65.0.3152.119 Safari/537.36" 3548 **3/3548019**
78.128.60.112 - - [15/May/2023:21:34:00 -0700] "POST /wp-admin/admin-ajax.php HTTP/1.1" 200 63 "-" "Mozilla/5.0 (Windows NT 6.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/65.0.3152.119 Safari/537.36" 444 **0/444932**
78.128.60.112 - - [15/May/2023:21:34:01 -0700] "POST /wp-admin/admin-ajax.php HTTP/1.1" 200 63 "-" "Mozilla/5.0 (Windows NT 6.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/65.0.3152.119 Safari/537.36" 430 **0/430144**
Thankfully the responsible party never gained access because I have code 2FA activated but it was definitely a frightening situation.
Since the attack, I have had attempts by some additional IPs to access the site using that unique admin username. Those IPs are:
84.19.30.243
37.9.171.155
147.135.128.179
87.229.111.207
12:04 pm
Hi Kenny,
Thanks for sharing this data! Sorry to hear your site was targeted by this, but also really glad to hear you had 2FA enabled which prevented any further escalation. Definitely a great example of why all site owners should have 2FA enabled on their sites. The attacker may have obtained your username from the /wp-json/wp/v2/users endpoint that may supply the username of any author who has created a post.
12:38 pm
Good evening,
Are the admin accounts created with this exploit random @outlook.com e-mail adress
with a creation date far in the past?
Best regards,
Henk
4:55 am
Hi Henk,
As of right now, we do not have any evidence to support that admin accounts are being created. This vulnerability will reset an admin user accounts password, and it does not create any new accounts. However, with that said, it sounds like the admin accounts appearing on your site may have been added via means outside of the standard user creation process.
1:25 pm
We encountered a similar situation where new admin accounts were created during the time of the attack. Although it's possible that these accounts are not directly related to the current attack, their creation coincided with the incident.
8:42 am
Hi Henk.
I noticed this sort of activity recently – Customer accounts created with random Outlook accounts in the past and missing 'First Name' and 'Last Name' fields. They seemed to originate from similar IP addresses to ones listed above. Some of these Customer accounts were then successfully changed from Customer to Admin roles. I'm not sure how the accounts were created though. I recommend installing WP Activity Log to keep an eye on it and blocking any malicious IPs.
Best regards,
Gordon